# Hacker News Top 30 — 2026-04-28
Generated on 2026-04-28 03:27 UTC
## [HN-TITLE] 1. Talkie: a 13B vintage language model from 1930
- **Source**: [https://talkie-lm.com/introducing-talkie](https://talkie-lm.com/introducing-talkie)
- **Site**: talkie-lm.com
- **Author**: Nick Levine, David Duvenaud, Alec Radford
- **Submitted**: 2026-04-27 21:55 UTC (Hacker News)
- **HN activity**: 128 points · [39 comments](https://news.ycombinator.com/item?id=47927903)
- **Length**: 2.4K words (~11 min read)
- **Language**: en
April 2026
This is a 24/7 live feed of Claude Sonnet 4.6 prompting [talkie-1930-13b-it](https://huggingface.co/talkie-lm/talkie-1930-13b-it) in order to explore its knowledge, capabilities, and inclinations. talkie’s outputs reflect the culture and values of the texts it was trained on, not the views of its authors.
## Why vintage language models?
Have you ever daydreamed about talking to someone from the past? What would you ask someone with no knowledge of the modern world? What would they ask *you*? While we don’t have time machines yet, we can simulate this experience by training, in Owain Evans’s phrase, [‘vintage’ language models](https://owainevans.github.io/talk-transcript.html): LMs trained only on historical text.
These models are fascinating conversation partners (watch Claude prompt talkie, our 13B 1930 LM, in the widget above). But we are also excited by the possibility that the careful study of the behaviors and capabilities of vintage LMs will advance our understanding of AI in general.
Figure 1. In an early attempt to understand a vintage model’s anticipation of the future, we took nearly 5,000 historical event descriptions from the *New York Times’s* [“On This Day” feature](https://archive.nytimes.com/learning.blogs.nytimes.com/on-this-day/), calculated their surprisingness (measured as bits per byte of text) to our 13B model trained exclusively on pre-1931 text, and binned by decade.
For example, we can evaluate LMs’ ability to predict the future. Inspired by Calcifer Computing’s work on [Temporal Language Models](https://www.calcifercomputing.com/reports/tlm), we calculated the surprisingness of short descriptions of historical events to a 13B model trained on pre-1931 text (Figure 1). We can see an increase after the knowledge cutoff, particularly pronounced in the 1950s and 1960s, followed by a plateau. We will continue to develop evals to measure with greater confidence how forecasting performance improves with model size and decays at longer horizons. Training larger vintage language models will allow us to uncover these scaling trends.
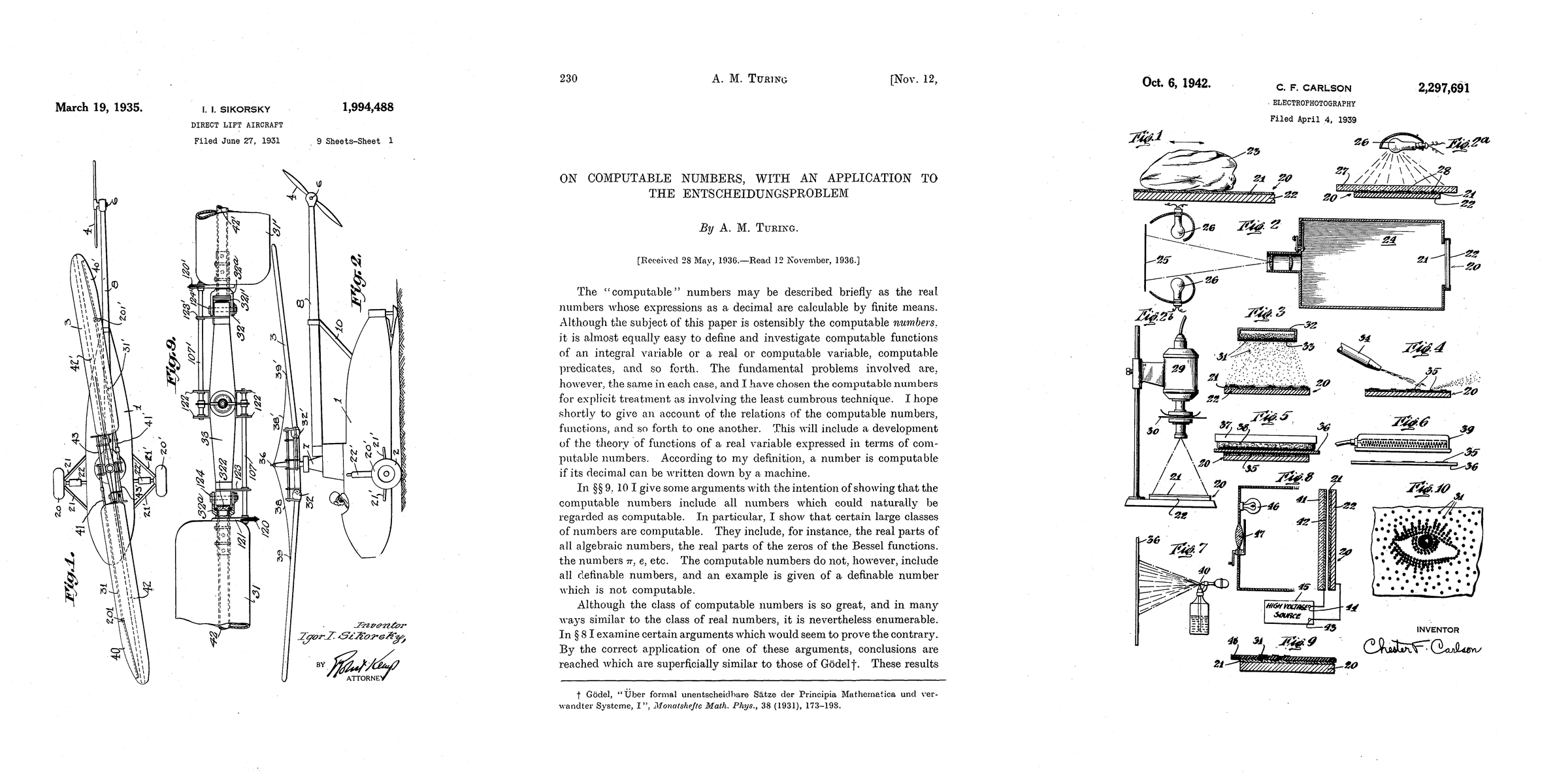
Figure 2. Patents and a paper published after talkie’s knowledge cutoff. Left to right: helicopter patent (Sikorsky, 1935), Turing machines paper (Turing, 1936), xerography patent (Carlson, 1942).
Similarly, we can test LMs’ abilities to come up with new ideas by seeing if they can arrive at inventions or scientific discoveries we know would arise after their knowledge cutoffs, such as those pictured in Figure 2. As Demis Hassabis has asked, could a model trained up to 1911 independently discover General Relativity, as Einstein did in 1915?
Figure 3. We gave a Python programming test ([HumanEval](https://github.com/openai/human-eval)) to a series of pairs of vintage models (trained on pre-1931 text) and modern models (trained on the web), which have the same architecture. Left: This chart shows what percentage of problems each model would get right at least once, given 100 chances and randomly chosen Python functions as examples to learn from in-context. Right: An example of a successful solution to a Python coding problem produced by a vintage language model. The model had access to several other in-context examples to learn from.
[Contamination](https://arxiv.org/abs/2602.12413) is a persistent problem for language models and causes us to overestimate the capabilities of LMs. Vintage LMs are contamination-free by construction, enabling unique generalization experiments, like examining whether a model with no knowledge of digital computers can learn to code in a modern programming language. Figure 3 (left-hand side) shows an early example of such a test, measuring how well models trained on pre-1931 text can, when given a few demonstration examples of [Python programs](https://github.com/openai/human-eval), write new correct programs. While vintage models dramatically underperform models trained on web data (which includes code), we’ve found that they are slowly but steadily improving at this task with scale.
There is still a long way to go before this capability is notable, however. All correct solutions generated by the vintage models are simple one-line programs (such as adding two inputs), or small modifications to in-context example programs. For instance, our model implemented the decoding function of a rotation cipher when [given the encoding function](https://huggingface.co/datasets/openai/openai_humaneval/viewer/openai_humaneval/test?row=50). Although the solution (Figure 3, right-hand side) is only a single character edit (swapping an addition for a subtraction), this success suggests an understanding of inverse functions. We hope LMs with early knowledge cutoffs help the research community understand how well LMs can generalize beyond their pre-training data.
Vintage language models could also teach us about the impact of data diversity in AI development. While modern models vary in disposition, capability, and behavior, they are all closely related to one another by having been trained, whether directly or indirectly (via distillation and synthetic data), on the web. How does this shape and constrain what they are? How much of what we think we know about LMs is about human language and culture in general, or about this one dataset—the web—in particular? Training on different sources may lead to very different kinds of models being created. Studying the ways in which they are similar and different could improve our understanding of language model personas, behaviors, and dispositions.
## Introducing talkie
We have been excited to see a proliferation of vintage LM projects, including [Ranke-4B](https://github.com/DGoettlich/history-llms/tree/main), [Mr. Chatterbox](https://www.estragon.news/mr-chatterbox-or-the-modern-prometheus/), and [Machina Mirabilis](https://michaelhla.com/blog/machina-mirabilis.html).
Alongside these efforts, we introduce [talkie-1930-13b-base](https://huggingface.co/talkie-lm/talkie-1930-13b-base), a 13B language model trained on 260B tokens of historical pre-1931 English text. Additionally, we present a post-trained [checkpoint](https://huggingface.co/talkie-lm/talkie-1930-13b-it) turning our base model into a conversation partner without relying on modern chat transcripts or instruction-tuning data.
talkie is the largest vintage language model we are aware of, and we plan to continue scaling significantly. As a next step, we are training a GPT-3-level model, which we hope to release this summer. A preliminary estimate also suggests we can grow our corpus to well over a trillion tokens of historical text, which should be sufficient to create a GPT-3.5 level model—similar in capability to the original ChatGPT.
## Benchmarking an LM from 1930
Figure 4. Evaluation accuracy vs. training compute for talkie-1930 (Vintage LM) and its [modern twin trained on FineWeb](https://huggingface.co/talkie-lm/talkie-web-13b-base). The vintage model underperforms the modern model on knowledge evals. Filtering out questions anachronistic from the perspective of 1930 roughly halves the performance gap between the vintage and modern models.
To contextualize talkie’s capabilities, we built a “[modern twin](https://huggingface.co/talkie-lm/talkie-web-13b-base)” that is identical architecturally but trained on modern web data (FineWeb) instead of pre-1931 text. On average, talkie underperforms its modern counterpart in standard LM evaluations, even after correcting for question anachronism, despite being trained with the same number of FLOPs (see Figure 4). But we have been encouraged by its similar performance on core language understanding and numeracy tasks.
We suspect a combination of differences in data quality (poor optical character recognition) and corpus subject matter distribution explains why talkie-1930 underperforms on some benchmarks. To maximize the compute efficiency of future vintage language model training, we are developing a vintage optical character recognition (OCR) system to improve the quality of transcription of historical text.
## Collecting vintage data
Piggybacking off the invaluable work of organizations like the [Institutional Data Initiative](https://huggingface.co/datasets/institutional/institutional-books-1.0) and the [Internet Archive](https://archive.org/about/) and efforts like [Common Pile](https://huggingface.co/common-pile), we have collected hundreds of billions of pre-1931 English-language tokens. These include books, newspapers, periodicals, scientific journals, patents, and case law. We chose the end of 1930 as the cutoff date because that is when works enter the public domain in the United States. For this version of the model, we also limited ourselves to primarily English-language texts, because validating the data pipeline requires deep familiarity with source documents, and we are native English speakers. But multilingual corpus expansion is a high priority, both to increase the size of the corpus and the diversity of perspectives it represents.
## Training vintage language models
Developing vintage language models presents unique challenges. Here, we discuss some of them in brief. We will follow up in greater detail in the coming months as we continue our research.
### Temporal leakage
Who was president of the United States in 1936, and what were the most significant pieces of legislation he signed?
Franklin D. Roosevelt was president of the United States from 1933 to 1937. The most important legislation signed by him was the National Recovery Act of 1933; the Agricultural Adjustment Act of 1935; and the Emergency Banking Act of 1935 (amended in 1936).
Figure 5. talkie-1930-13b’s knowledge of the Roosevelt presidency and New Deal is an example of imperfect filtering of the pre-training corpus.
The most important objective when training vintage language models is that no data leaks into the training corpus from after the intended knowledge cutoff (in our case, December 31st, 1930). There are several ways this can happen, such as including modern documents with faulty date metadata, or old documents with post hoc anachronistic insertions like editorial introductions or footnotes.
For talkie-1930, we developed a document-level n-gram-based anachronism classifier and used it to filter the pre-training corpus. However, this was not perfect. An earlier 7B version of talkie clearly knew about the Roosevelt presidency and New Deal legislation (Figure 5). talkie-1930-13b is additionally aware of some details related to World War II and the immediate postwar order (the United Nations and the division of Germany). For future versions of the model, we are developing new techniques for leakage detection and filtering using more advanced classifiers.
### Data quality
Figure 6. OCR errors reduce language model learning efficiency. Left: Training LMs on pre-1931 texts transcribed using conventional OCR systems only shows 30% of the learning efficiency of a model trained on human-transcribed versions of the same texts. Regex cleaning of the OCR’d text recovers some performance. Right: Example of a messy machine transcription of *The Wonderful Wizard of Oz* (Baum, 1899).
Data quality is an important issue for all machine learning experiments. It is a special challenge when training vintage language models. Because there was no digital publishing in 1930, all text in our dataset had to be transcribed from a physical source, which introduces a form of noise not seen in natively digital text. While OCR was an early success story of machine learning and computer vision, the classic OCR systems often used to transcribe historical documents struggle on all but the simplest layouts and cleanest scans. Modern VLM-based systems have higher accuracy, but we have found they are prone to hallucinate modern facts into our corpus, poisoning the exercise.
In controlled experiments, we have found that when training an LM on pre-1931 texts transcribed using conventional OCR systems, for a given amount of compute, they only achieve 30% of the performance of a model trained on human-transcribed versions of the same texts (see Figure 6). Simple regex cleaning brings that number up to 70%—still a large discrepancy. We aim to shrink the remaining gap in performance by retranscribing the talkie corpus using our vintage OCR system.
### Vintage post-training
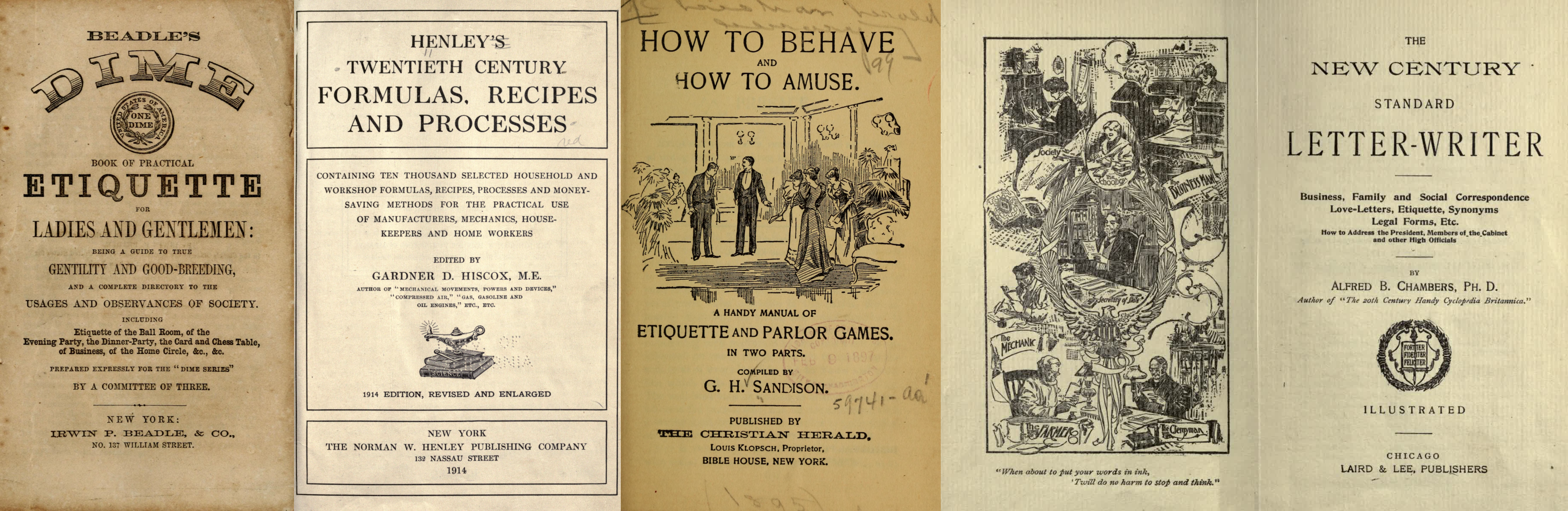
Figure 7. Examples of historical reference texts with regular structure used for post-training. Left to right: etiquette manual (Beadle, 1859), practical knowledge book (Henley, 1914), parlor guide (Sandison, c. 1895), letter-writing manual (Chambers, 1900).
The lack of ready-made post-training data is another significant challenge. Fine-tuning our base model on off-the-shelf instruction-response pairs would bake in anachronistic knowledge, style, and expectations of what a chat assistant ought to be like. Rather than attempting to filter out these biases, we built a post-training pipeline from scratch.
First, we generated instruction-response pairs from historical texts with regular structure, such as etiquette manuals, letter-writing manuals, cookbooks, dictionaries, encyclopedias, and poetry and fable collections (see Figure 7), and fine-tuned our base model on them using a simple chat format.
Next, to improve instruction-following abilities, we generated synthetic prompts covering different types of tasks, such as summarizing documents, responding to direct information requests, and continuing multi-turn conversations coherently. We then ran online direct preference optimization on rollouts generated from these prompts, using Claude Sonnet 4.6 as a judge. Over the course of training, on a held-out eval set, the judge’s average instruction-following rating of talkie’s responses increased from 2.0 to 3.4 (on a five-point scale).
Finally, we did another round of supervised fine-tuning, this time on rejection-sampled multi-turn synthetic chats between Claude Opus 4.6 and talkie, to smooth out persistent rough edges in its conversational abilities.
While we have tried to post-train talkie free from modern influence, reinforcement learning with AI feedback inevitably shapes talkie’s behavior anachronistically. (The 7B version of talkie emerged from RL speaking in listicles.) As we scale up, we hope to be able to use our vintage base models themselves as judges to enable a fully bootstrapped era-appropriate post-training pipeline.
## Scaling talkie
We plan to scale talkie rapidly in the coming months. This will entail:
- Increasing the size of our English-language corpus, and expanding it beyond English.
- Re-OCR’ing as much of pre-1931 text as is feasible using our new OCR system.
- Strengthening the leakage detection pipeline by developing new anachronism classification techniques.
- Expanding and refining the vintage post-training pipeline in collaboration with historians, including by developing methodologies for constructing accurate historical personas.
## Join us
We are excited to collaborate with researchers and institutions to build the next generation of vintage language models. Please [get in touch](mailto:hello@talkie-lm.com).
- Are you a researcher or institution with historical texts? We’d love to discuss how we can help make them accessible to researchers and readers, including by applying our OCR model.
- Are you an individual or institution interested in supporting vintage language model development with funding or compute? We can likely use either, or put you in touch with other teams working in the space.
- Are you an academic in the humanities? We are excited to discuss how vintage language models, and the data and infrastructure used to train them, could be useful for your research.
- Are you an AI researcher? We would love to support and collaborate on research on training and [studying vintage language models](https://github.com/talkie-lm/talkie).
- Are you an artist or writer? We think vintage language models could be fruitful tools to [experiment with](https://github.com/talkie-lm/talkie).
## Content considerations
talkie reflects the culture and values of the texts it was trained on. As such, it can produce outputs that will be offensive to users.
## Acknowledgements
Thanks to Coefficient Giving and Anthropic for support with funding and compute.
For helpful discussions, we thank Pranav Anand, Benjamin Breen, Catherine Brobston, Collin Burns, Matteo Cargnelutti, Mackenzie Cooley, Brandon Duderstadt, Owain Evans, Chloë Farr, Ryan Greenblatt, Michael Hla, Mark Humphries, Sam Klein, Greg Leppert, Jack Lindsey, Christina Lu, Seoirse Murray, Jake Naviasky, Krishna Patel, Ethan Perez, Puria Radmard, Ludwig Schmidt, Buck Shlegeris, Benjamin Sturgeon, Daniel Tan, Ross Taylor, Cam Tice, Trip Venturella, Merlijn Wajer, and Tao Xu.
## Citation
```
@article{levine2026talkie,
title={Introducing talkie: a 13B vintage language model from 1930},
author={Levine, Nick and Duvenaud, David and Radford, Alec},
year={2026},
month={April},
url={https://talkie-lm.com/introducing-talkie}
}
```
---
## [HN-TITLE] 2. Microsoft and OpenAI end their exclusive and revenue-sharing deal
- **Source**: [https://www.bloomberg.com/news/articles/2026-04-27/microsoft-to-stop-sharing-revenue-with-main-ai-partner-openai](https://www.bloomberg.com/news/articles/2026-04-27/microsoft-to-stop-sharing-revenue-with-main-ai-partner-openai)
- **Site**: Bloomberg
- **Author**: Matt Day
- **Published**: 2026-04-27
- **HN activity**: 779 points · [677 comments](https://news.ycombinator.com/item?id=47921248)
- **Length**: 133 words (~1 min read)
- **Language**: en
AI
OpenAI CEO Sam Altman, left, speaks with Microsoft Chief Technology Officer Kevin Scott during the Microsoft Build conference in Seattle in 2024.
Photographer: Jason Redmond/AFP/Getty Images
April 27, 2026 at 1:14 PM UTC
Updated on
April 27, 2026 at 2:36 PM UTC
[Microsoft Corp.](https://www.bloomberg.com/quote/MSFT:US) and OpenAI have agreed to drop the software giant’s exclusive right to sell the startup’s AI models, opening the door for the ChatGPT maker to pursue deals with cloud-computing rivals like [Amazon.com Inc.](https://www.bloomberg.com/quote/AMZN:US)
In exchange for ending that exclusivity — which helped boost Microsoft’s cloud sales in the early years of the AI boom — the world’s largest software maker will no longer pay a revenue share on OpenAI products it resells on its cloud. The two companies announced the revised deal in a joint [statement](https://openai.com/index/next-phase-of-microsoft-partnership/ "The next phase of the Microsoft OpenAI partnership") on Monday.
---
## [HN-TITLE] 3. Integrated by Design
- **Source**: [https://vivianvoss.net/blog/integrated-by-design-launch](https://vivianvoss.net/blog/integrated-by-design-launch)
- **Site**: vivianvoss.net
- **Submitter**: vermaden (Hacker News)
- **Submitted**: 2026-04-27 23:14 UTC (Hacker News)
- **HN activity**: 75 points · [27 comments](https://news.ycombinator.com/item?id=47928554)
> no extractable content
---
## [HN-TITLE] 4. Meetings are forcing functions
- **Source**: [https://www.mooreds.com/wordpress/archives/3734](https://www.mooreds.com/wordpress/archives/3734)
- **Site**: mooreds.com
- **Submitter**: zdw (Hacker News)
- **Submitted**: 2026-04-26 03:12 UTC (Hacker News)
- **HN activity**: 67 points · [28 comments](https://news.ycombinator.com/item?id=47906942)
- **Length**: 274 words (~2 min read)
- **Language**: en-US
A recurring meeting serves as a powerful forcing function for long-running projects.
Many organizations face a common challenge: a complex project that requires effort and perspectives from multiple people, moves through definition and execution phases, and unfolds over weeks, months, or years. But one where the tasks to accomplish the project are not anyone’s full-time job.
Everyone has other obligations, fires to put out, and emails to answer. It’s easy for long-term strategic, high-impact work to sink to the bottom of everyone’s todo list.
One effective solution is to schedule a standing meeting. Whether in person or video, it doesn’t matter. The key to making progress is maintaining an agenda and, critically, opening each meeting by reviewing the to-dos from the previous one. This creates pressure on everyone to make progress. When people know they’ll be asked “what’s the status of X that we talked about last week?” at an upcoming meeting, it is easier, though not easy, to carve out time for that work amid the daily chaos.
This approach works across organizational boundaries too. If you’re a consulting firm, a regular cadence of meetings with your client is especially valuable. You’re motivated to deliver., but people on the client’s team may be less so. A meeting where you consistently show progress while they haven’t made any creates gentle but real accountability.
If you’re managing a large, complex, multi-person effort, consider the standing meeting. As far as schedule, weekly, bi-weekly, or monthly all have worked for me in the past. Pick whatever fits the urgency.
Use a meeting as a forcing function to ensure people actually make time to move the project forward.
---
## [HN-TITLE] 5. Ted Nyman – High Performance Git
- **Source**: [https://gitperf.com/](https://gitperf.com/)
- **Site**: gitperf.com
- **Submitter**: gnabgib (Hacker News)
- **Submitted**: 2026-04-28 00:32 UTC (Hacker News)
- **HN activity**: 30 points · [6 comments](https://news.ycombinator.com/item?id=47929035)
- **Length**: 321 words (~2 min read)
- **Language**: en

Git looks like a version-control tool. It is also a content-addressed database, a filesystem cache, a graph walker, and a transfer protocol.
This book is about those layers and the performance costs of each one. It starts with objects, refs, the index, and history traversal, then moves outward into packfiles, maintenance, sparse working trees, partial clone, transport, repository scale, diagnosis, configuration, and recovery.
It is written for engineers who need Git to stay fast as repositories, histories, and teams get larger: build and CI engineers, monorepo owners, developer-experience teams, and the people who wind up debugging strange Git behavior when the easy explanations stop working.
* * *
### Section 0 · Introduction
0. [Introduction](https://gitperf.com/chapter-00.html)
### Section I · Foundations
Why Git gets slow, what Git stores, and how refs and the index steer through it.
1. [Why Git Performance Matters](https://gitperf.com/chapter-01.html)
2. [Git's Core Data Model](https://gitperf.com/chapter-02.html)
3. [Refs, HEAD, Reflogs, Index](https://gitperf.com/chapter-03.html)
### Section II · History and Rewrite
How Git walks history and how rewrite commands reshape it without mutating commits.
4. [Revisions and History Traversal](https://gitperf.com/chapter-04.html)
5. [Merge, Rebase, Cherry-Pick, Rewrite](https://gitperf.com/chapter-05.html)
### Section III · Storage and Local Scale
Object storage, index cost, maintenance, and the techniques that shrink local state.
06. [Loose Objects, Packfiles, Delta Compression](https://gitperf.com/chapter-06.html)
07. [The Index as a Performance Structure](https://gitperf.com/chapter-07.html)
08. [Commit-Graph, Bloom Filters, MIDX, Bitmaps](https://gitperf.com/chapter-08.html)
09. [Git GC and Maintenance](https://gitperf.com/chapter-09.html)
10. [Sparse-Checkout and Sparse-Index](https://gitperf.com/chapter-10.html)
### Section IV · Large-Repo Operations, Transport, and Scale
Clone shape, transfer policy, parallel work with worktrees, repository size, and ref scale.
11. [Partial Clone and Promisor Remotes](https://gitperf.com/chapter-11.html)
12. [Scalar, Prefetch, Large Repositories](https://gitperf.com/chapter-12.html)
13. [Worktrees](https://gitperf.com/chapter-13.html)
14. [Clone, Fetch, Push, Protocol v2](https://gitperf.com/chapter-14.html)
15. [Bundles and Bundle URIs](https://gitperf.com/chapter-15.html)
16. [Reducing Repository Size](https://gitperf.com/chapter-16.html)
17. [Large Ref Sets: Files, Packed-Refs, Reftable, and `git refs`](https://gitperf.com/chapter-17.html)
### Section V · Diagnosis and Recovery
How to instrument Git, find the slow layer, apply high-leverage settings, and recover when the repository is actually wrong.
18. [Instrumenting Git](https://gitperf.com/chapter-18.html)
19. [Finding and Fixing Slow Git](https://gitperf.com/chapter-19.html)
20. [Configuration Playbook](https://gitperf.com/chapter-20.html)
21. [Recovery and Repair](https://gitperf.com/chapter-21.html)
### Back Matter
- [Epilogue: Git in the Agent Loop](https://gitperf.com/epilogue.html)
- [Appendix: Compatibility Guidance](https://gitperf.com/appendix-version-requirements.html)
- [Appendix: Approaches to Virtualized Working Trees](https://gitperf.com/appendix-virtualized-working-trees.html)
- [Glossary of Git Terms](https://gitperf.com/glossary.html)
---
## [HN-TITLE] 6. Three men are facing charges in Toronto SMS Blaster arrests
- **Source**: [https://www.tps.ca/media-centre/stories/unprecedented-sms-blaster-arrests/](https://www.tps.ca/media-centre/stories/unprecedented-sms-blaster-arrests/)
- **Site**: tps.ca
- **Submitter**: gnabgib (Hacker News)
- **Submitted**: 2026-04-27 20:44 UTC (Hacker News)
- **HN activity**: 119 points · [52 comments](https://news.ycombinator.com/item?id=47927070)
> scrape failed: http 403
---
## [HN-TITLE] 7. Is my blue your blue?
- **Source**: [https://ismy.blue/](https://ismy.blue/)
- **Site**: ismy.blue
- **Submitter**: theogravity (Hacker News)
- **Submitted**: 2026-04-27 20:24 UTC (Hacker News)
- **HN activity**: 380 points · [256 comments](https://news.ycombinator.com/item?id=47926861)
- **Language**: en
> no extractable content
---
## [HN-TITLE] 8. Mo RAM, Mo Problems (2025)
- **Source**: [https://fabiensanglard.net/curse/](https://fabiensanglard.net/curse/)
- **Site**: fabiensanglard.net
- **Submitter**: blfr (Hacker News)
- **Submitted**: 2026-04-25 15:41 UTC (Hacker News)
- **HN activity**: 25 points · [4 comments](https://news.ycombinator.com/item?id=47902269)
- **Length**: 537 words (~3 min read)
Feb 16, 2025
Mo RAM, mo problems
* * *
As a retro-computer enthusiast, it seems that parts are either insanely expensive or dirt cheap. If the first case has obvious problems, the second can also lead to issues.
When I built the [Quake PC](https://fabiensanglard.net/quake_pc), the motherboard and HDD were worth their weight in gold. But the price of RAM modules was ridiculously low. So I maxed out by buying $40,000 worth of 1997 SDRAM, namely 384 MiB, for the price of $60.
From 44 fps to 33 fps
* * *
After I got the machine working, I ran benchmarks for weeks. I was constantly swapping video-cards, changing RAM types (SDRAM, EDO), adding RAM, removing RAM, and testing different CPUs. The CPU in my collection that ran Quake the best was the Pentium MM 233MHz clocking demo1 at **44.6 fps**. That figure was consistent with benchmarks of the era.
I wrote an [article about winquake](https://fabiensanglard.net/winquake) then took a break from 1997. A month later I had the idea to measure Michael Abrash assembly optimizations. I ran the same benchmark again. But this time I measured **33 fps**. That was nearly 25% slower. What happened?
Troubleshooting
* * *
I tried pretty much everything I could think of. I swapped the graphic card, removed all the 3D accelerators, updated the drivers, downgraded the drivers, wiped the whole system, re-installed everything, double checked that I was still using the MMX 233Mhz, and verified the frequency multiplier. Still **33 fps**.
Did a RAM module go bad? I tried to remove one of them. **33 fps**. Remove a second one (leaving only one). Now the game ran at **44 fps**. Two modules going bad? Hm, that seems weird. I tried to swap modules, leaving only one in the machine. All of them ran the game a **44 fps**. Only when two of more are in the machine, the framerate drops back to **33 fps**.
Epiphany
* * *
I vaguely remembered something about having too much RAM from the excellent *Upgrading and Repairing PCs 10th edition*.
> That last issue is one that many people are not aware of. The 430FX chipset can only cache up to 64M of main memory. This means that if you install more than 64M of RAM in your system, performance will suffer greatly.
>
> Now, many think this won’t be that much of a problem—after all, they don't normally run enough software to load past the first 64M anyway. That is another misunderstanding, because Windows 95 and NT load from the top down.
>
> This means, for example, that if you install 96M of RAM (one 64M and one 32M bank), then virtually all of your software, including the main operating system, will be loading into the non-cached region above 64M. Only if you use more than 32M would you begin to see an improvement in performance. tem.
>
> - Upgrading and Repairing PCs 10th edition
My motherboard, an XA100, is from 1998 and advertised[\[1\]](#footnote_1) as supporting caching of 512MiB, but there is clearly something amiss there. It seems it actually can only cache in the neighborhood of 128 MiB. Which means any amount over that, made everything run without a L2 cache!
And that is the story of how I made that PC faster, by removing RAM.
References
* * *
* * *
\*
---
## [HN-TITLE] 9. The quiet resurgence of RF engineering
- **Source**: [https://atempleton.bearblog.dev/quiet-resurgence-of-rf-engineering/](https://atempleton.bearblog.dev/quiet-resurgence-of-rf-engineering/)
- **Site**: Anthony T's Blog
- **Submitter**: merlinq (Hacker News)
- **Submitted**: 2026-04-25 18:25 UTC (Hacker News)
- **HN activity**: 153 points · [84 comments](https://news.ycombinator.com/item?id=47903439)
- **Length**: 1.8K words (~9 min read)
- **Language**: en
*14 Apr, 2026*
I've worked in the aerospace industry for the past 8 years, and for most of that time I felt like I could confidently say that RF engineering felt like it was a quiet, non evolving field. The advice I heard early on, and that I watched a lot of other people follow, was to go into software. Machine learning, cloud infrastructure, web development. That's where the growth was, that's where the money was, and honestly, that's where most new graduates went (myself included at the time). I studied Information Systems in college, not electrical engineering. RF was nowhere on my radar.
But aerospace has a way of pulling you into hardware whether you planned on it or not. I started my career at NASA, building telemetry platforms, ETL pipelines, and spacecraft visualization tools. Pure software work. Then I moved to a private aerospace company. Much smaller than NASA (approx 130 employees at the time I joined), and it required me to wear a ton of hats to work on ground systems. That's where things shifted. When you're responsible for ground station services, even when most of it now is *software defined* you can't stay in the software lane entirely. I found myself doing link budget analysis, troubleshooting RF anomalies, and developing a working understanding of the RF hardware chain that I never expected to need.
That experience is part of why I've been paying attention to what's happening in RF more broadly. I've been feeling a shift over the past several years — more demand, fewer people, and more urgency from the companies I talk to. RF engineering is not only alive, it's rebounding in a significant way. I wanted to dig into whether my gut feeling here is actually backed by data, or if I'm just seeing what I want to see from inside the aerospace bubble.
## What Actually Happened to RF
To be fair to the people who called RF a shrinking field, they weren't wrong, at least for a stretch. After the dot-com bust in the early 2000s, the telecom industry consolidated hard. Companies merged, manufacturing moved offshore, and a lot of RF design work either disappeared or got absorbed into a handful of large defense contractors. The broader electrical engineering job market stagnated. [Electronic Design](https://www.electronicdesign.com/technologies/embedded/article/21255051/electronic-design-electronics-and-electrical-engineering-jobs-on-the-declinecan-they-be-saved) has documented this trend not just for RF, but across EE as a whole. I feel confident that if the field as a whole is shrinking, then the subfield of RF was also in decline.
And then software exploded. The engineers who might've gone into EE or RF design a generation earlier went down the software "FAANG" route instead. University enrollment in RF specific coursework drifted down. Though I'll be honest, hard numbers on this are annoyingly hard to find so this is more of my gut assumption. What we do know is that today, companies [openly describe the difficulty](https://filtronic.com/blogs_challenges-of-recruiting-rf-engineers/) of recruiting RF engineers, pointing to a generation that chose software over EE.
But here's the thing that gets missed in the narrative: it never actually went away. The defense sector has been keeping it alive this entire time. Raytheon, Lockheed Martin, Northrop Grumman, these companies never stopped hiring people who understand beam patterns, power amplifiers, and antenna design. The majority of RF engineering job postings have historically come from aerospace and defense. RF didn't die. It just receded from the civilian sector while quietly remaining essential to national security and defense.
## So What Changed
The resurgence didn't come from one place. It's coming from several industries all hitting the same wall at roughly the same time; a shortage of engineers who can work at the hardware level.
### The Space Boom
This is the one I see most directly in my work, and it *feels* the most dramatic. In 2015, roughly [260 spacecraft were launched](https://ourworldindata.org/grapher/yearly-number-of-objects-launched-into-outer-space) into space globally. By 2024, that number hit approximately 2,695. A 10x increase in under a decade. The overwhelming majority of that growth came from commercial constellations, with SpaceX's Starlink deploying over 1,500 satellites in 2023 alone.
Every single one of those satellites needs RF hardware. Starlink operates in Ku-band for user links and Ka-band for gateways, with V-band planned for Starlink V2. Kuiper and OneWeb follow similar architectures in Ka-band. Each spacecraft carries transceivers, antennas, filters, and amplifiers — and each ground station that talks to them needs the same. The amount of RF hardware per spacecraft adds up fast, and the launch cadence isn't slowing down.
The money tells the same story. The global space economy hit a record [$613 billion in 2024](https://www.spacefoundation.org/2025/07/22/the-space-report-2025-q2/), with commercial making up roughly 78% of that. The [space based RF market](https://www.openpr.com/news/4298716/space-based-rf-and-microwave-technology-market-size-share) alone was valued at $18.6 billion and is projected to nearly double by 2033.
And it's not just commercial. On the defense side, the Space Development Agency is building the [Proliferated Warfighter Space Architecture](https://payloadspace.com/ndsa-explainer/) — a LEO constellation targeting 500+ satellites. Only a few dozen are on orbit today, but nearly $35 billion has been committed through 2029. Even with the growing push toward optical links, these spacecraft still carry RF communications hardware and telemetry payloads, and that is unlikely to change anytime soon.
### 5G Wide Adoption
I think 5G's impact on RF demand is genuinely understated. A typical 4G base station has 2 or 4 transmit-receive chains. A 5G MIMO radio integrates anywhere from 64 to 256. That's an 8x to 16x increase in the power amplifiers, low-noise amplifiers, and antenna switches needed per installation. Multiply that across [642 operators and 374 commercial launches](https://gsacom.com/technology/5g/), and you start to see why the [RF component market](https://www.mordorintelligence.com/industry-reports/rf-components-market) is pushing toward $50 billion with no signs of stoppage.
The design challenges make it worse. Millimeter wave frequencies introduce path loss that demands arrays with manufacturing tolerances at the millimeter scale. Additionally, thermal management, ex. dissipating 300+ watts from tower-mounted hardware with passive cooling, isn't something you can solve reliably in software.
### 6G Is Already In The Works
It's early, but 6G isn't vaporware. [3GPP](https://www.3gpp.org/specifications-technologies/releases/release-20) has been actively working on 6G study items since 2024, with first specifications targeted for late 2028 and commercial deployments expected around 2030. The EU, South Korea, and major telecom players like Ericsson, Nokia, and Samsung are all investing heavily into this research.
The RF challenges are genuinely new territory. Sub-terahertz frequencies and [integrated sensing and communication](https://www.ericsson.com/en/blog/2024/6/integrated-sensing-and-communication) (ISAC), which 3GPP officially scoped into 6G in the middle of last year, push well beyond what current design tools can handle. Worth noting though — the original vision for sub-THz has already been [scaled back](https://the-mobile-network.com/2026/04/6g-reality-check-and-update/) from outdoor cellular to mostly short-range indoor use cases like data centers and factories. But even with a narrower scope, all of this research eventually has to become hardware, and the people who know how to do that are already stretched thin.
### The "Drivers" That Don't Get Headlines
Space and cellular seem to dominate the conversation, but there are quieter contributors that I think are what make this feeling more durable rather than cyclical.
Automotive radar is a sneaky one. The EU now [mandates automatic emergency braking](https://spectrum.ieee.org/europe-mandates-automatic-emergency-braking) in all new vehicles and, while the regulation is *technically* sensor-agnostic, most implementations rely on radar. Every new car with adaptive cruise control or collision avoidance has RF hardware running on board. That market alone is projected to hit $7+ billion this year. Then there's Wi-Fi 7, operating across three bands simultaneously, and the ever expanding IoT landscape with over 21 billion connected devices as of 2025. Anything that communicates wirelessly needs RF work behind it, and that list just keeps growing.
## The Talent Shortage
What makes this an interesting pattern, is that the supply side is genuinely broken. [IEEE survey data](https://k2staffinginc.com/electrical-engineering-talent-shortages-how-recruiters-bridge-the-gap/) shows 73% of EE employers can't fill positions within six months, up from 45% five years ago. [EE Times](https://www.eetimes.com/engineer-demand-exposes-talent-gap-in-rf-development/) has reported specifically on the RF talent gap and its growing demand.
And it's not just direct competition for RF roles either. RF and semiconductor careers often pull from the same shrinking pool of EE graduates, and right now the semiconductor side is in a hiring frenzy of its own. The CHIPS Act has poured billions into domestic fab expansion, AI chip demand is exploding, and the semiconductor industry is projecting a [67,000 worker shortfall by 2030](https://www.semiconductors.org/chipping-away-assessing-and-addressing-the-labor-market-gap-facing-the-u-s-semiconductor-industry/). All of that competes directly with RF employers for the same talent. When everyone is fighting over the same small group of EE grads, RF companies, which tend to be smaller and less visible than the big chip fabs, often lose out.
Salaries reinforce this. Average RF engineer comp is pushing past $130K, with top-end design positions listing above $200K.
The real signal to me is what companies are doing about it. [Mini-Circuits](https://blog.minicircuits.com/bridging-the-gap-between-the-university-and-the-rf-industry/) and Keysight are investing directly in university partnerships because they can't wait for the academic pipeline to refresh itself. Baylor launched a new Graduate Certificate in Microwave/RF Engineering in 2024, one of the few new programs I've seen pop up, but I imagine it won't be the last. When industry starts building its own talent pipeline, that tells me the shortage isn't a blip.
## Looking Forward
I don't want to oversell this. I don't think RF is going to become a field with an insane growth pattern. [The BLS](https://www.bls.gov/ooh/architecture-and-engineering/electrical-and-electronics-engineers.htm) projects 7% growth for EE broadly, faster than average sure, but not a hockey stick. The demand is real, it's coming from multiple directions at once, and the supply is genuinely constrained.
My own path is a small version of this story. I came in as a software engineer and had to learn RF on the job because there wasn't someone else to hand it off to. I say this as someone who made that transition, you *absolutely* can learn enough RF to be effective in your role, and I'd encourage anyone in aerospace or wireless to do it (honestly it's a fun niche to get into anyway). But there's a difference between understanding link budgets and SDR anomalies versus designing a phased array from scratch. The latter takes years of dedicated focus. The underlying physics (electromagnetics, thermodynamics, materials science, manufacturing tolerances) don't reduce to algorithms. You have to build intuition for it, and that's not something you can shortcut.
I may one day expand on learning this stuff on the job and on the fly, but I do want to shoutout [PySDR](https://pysdr.org/). It's a free resource built exactly for software engineers. It uses Python as the bridge between hardware and software concepts, and starts with no RF knowledge assumptions from the beginning and doesn't spend a ton of time over explaining the math.
The people who stuck with RF through the lean years are now some of the most sought-after engineers I've come across. And for anyone trying to figure out where to focus, either as a primary discipline or as a secondary skill set like it was for me, I think RF is worth a serious look right now.
* * *
**Who Am I?**
Anthony Templeton is a software engineer passionate about high-performance computing and aerospace applications. You can connect with me on [LinkedIn](https://www.linkedin.com/in/anthony-f-templeton/) or check out more of my work on [GitHub](https://github.com/ATTron).
---
## [HN-TITLE] 10. Easyduino: Open Source PCB Devboards for KiCad
- **Source**: [https://github.com/Hanqaqa/Easyduino](https://github.com/Hanqaqa/Easyduino)
- **Site**: GitHub
- **Submitter**: Hanqaqa (Hacker News)
- **Submitted**: 2026-04-27 17:45 UTC (Hacker News)
- **HN activity**: 179 points · [27 comments](https://news.ycombinator.com/item?id=47924813)
- **Length**: 789 words (~4 min read)
- **Language**: en
## Easyduino: Repository of Open Source PCB Devboards for KiCad
[](#easyduino-repository-of-open-source-pcb-devboards-for-kicad)
The Easyduino project is an effort to easily dive into different PCB designs of the most popular microcontroller devboards like **Arduino, ESP32, Raspberry Pico and STM32 Bluepill** (more to come!). Using the free and Open Source Software [KiCad](https://www.kicad.org/) and adhering the best practices across the PCB and KiCad ecosystem. Also adding the much needed USB-C support!
[](https://github.com/Hanqaqa/Easyduino/blob/master/Assets/Isometric%20Photos/Collage_easyduino.jpg)
The project was born out of the necessity to unify the wide variety of software, languages and conventions used in the most popular devboards. For example Arduino Uno was developed in 2010, Italy, using Eagle. The ESP32 devboard was developed in 2016, China, using Altium. The Raspberry Pi Pico 2040 was developed around 2021 in the U.K. using KiCad and Altium...
## Available Development Boards
[](#available-development-boards)
[Easyduino UNO](https://github.com/Hanqaqa/Easyduino/tree/master/Atmega328p%20Arduino%20Uno) [Easyduino Nano](https://github.com/Hanqaqa/Easyduino/tree/master/Atmega328p%20Arduino%20Nano) [Easyduino ESP32](https://github.com/Hanqaqa/Easyduino/tree/master/ESP32) [](https://github.com/Hanqaqa/Easyduino/tree/master/Atmega328p%20Arduino%20Uno) [](https://github.com/Hanqaqa/Easyduino/tree/master/Atmega328p%20Arduino%20Nano) [](https://github.com/Hanqaqa/Easyduino/tree/master/ESP32)
[Easyduino ESP32 S3](https://github.com/Hanqaqa/Easyduino/tree/master/ESP32S3) [Easyduino Pi Pico](https://github.com/Hanqaqa/Easyduino/tree/master/Raspberry%20Pi%20Pico%202040) [Easyduino Bluepill STM32F103](https://github.com/Hanqaqa/Easyduino/tree/master/STM32F103%20Bluepill) [](https://github.com/Hanqaqa/Easyduino/tree/master/ESP32S3) [](https://github.com/Hanqaqa/Easyduino/tree/master/Raspberry%20Pi%20Pico%202040) [](https://github.com/Hanqaqa/Easyduino/tree/master/STM32F103%20Bluepill)
The outline, pinout, layout and components have been tried to be replicated with respect to the originals, in all of the boards. With various levels of success.
Some boards, like the Raspberry Pi Pico use 01005 components which are too expensive for the manufacturer to integrate in the PCB Aseembly line. Some other components like the original Arduino UNO USB to Serial converter, an Atmega16u2, were hard to come by during the development of this project ~January 2023, so more readily available options were chosen. All the differences with the original boards are explained inside the folder of each project in a readme file.
4 layers of copper have been used in all projects to simplify the wiring. Specifically the [JLC04161H-7628](https://jlcpcb.com/impedance) stackup.
The PCB constraints of the manufacturer JLCPCB are explained [here](https://github.com/Hanqaqa/Easyduino/tree/master/Assets/JLCPCB%20Constraints)
## Structure of each project
[](#structure-of-each-project)
Each project consists of:
- Main KiCad files (.kicad\_pro, .kicad\_sch...)
- A readme explaining the specifics of that project
- xxx.pretty or xxxlibraries folder which contains the non standard footprints or schematic parts used in the project (Some projects such as the Arduino UNO only use standard libraries, therefore these folders don't exist)
- The **Outputs** folder: All the data produced by the KiCad Jobset like Gerbers, STEPs, PDFs, ERC, BOM, CPLs...
- The ***ProductionFiles*** folder which includes files such as:
- BOM: This folder contains both the list of components and the Centroid File in JLCPB readable format
- ***Datasheets***: all the datasheets of the main components used in the project. Datasheets of easily replaceable components such as Resistors, Capacitors and LEDs are not given
- Gerbers: A zip file with all of the manufacturing gerber files such as Copper/Mask/Silkscreen layers
- PDFs: PDF and PNG files of the Schematic and PCB
- Photos: Some photos of the manufactured PCB as well as some renders
## Using the project
[](#using-the-project)
1. Install the latest version of [KiCad](https://www.kicad.org/)
2. If you already have KiCad installed, click the upper right button in this github page `<>Code`, click `Download ZIP`, extract the files in your desired folder. If you know how to use git, clone the repository
3. Double click on the xxx.kicad\_pro file inside any project and KiCad will start
This project was developed using KiCad v8.0.0, but has been updated and tested with KiCad v10. Including the creation of Jobsets which massively simplfies creating gerbers and BOMs.
Since this is a collection of projects, the new KiCad v10 Git utilities don't work properly with each project, forcing you to git add the whole project if you want to make a change.
If you'd rather just consult the schematics or the gerbers. They are located inside the **ProductionFiles** folder of each project. Inside the **PDFs** and **Gerber** folders.
## Contributing
[](#contributing)
If you spot any mistakes inside any of the projects. Either open an issue and I will try to correct it or fork and merge the correction.
If you plan on developing any other development boards and wish to merge into the project. Please try to use the same style and conventions as the original ones in the schematic. Positive voltages facing up, text being clearly readable, a references page, similar folder structure.
To do list:
- Order and test the v1.1 RP2040 board. (In v1.0 I mixed some pins in the Flash and couldn't boot up). Ordered. Awaiting arrival.
- Order and test the v1.1 ESP32S3 board. (In v1.0 I forgot to add PullUp and PullDown in RST and SUSPEND CP2102). Ordered. Awaiting arrival.
- Start developing a nRF52840 Dongle and RP2350A.
- Investigate other possible microcontrollers/SOCs to implement.
## Acknowledgments
[](#acknowledgments)
Thanks to [winsrrow](https://github.com/winsrrow) for providing KiCad tips and designing from the ground up the v1.1 RP2040 board.
## Licensing
[](#licensing)
This project is distributed under the [**CERN Open Hardware Licence Version 2 - Permissive**](https://github.com/Hanqaqa/Easyduino/blob/master/License.txt) which means **you are free to use any or all parts of this project with or without disclosing the source**, even for comercial projects. As long as you include a copy of the CERN OHLv2 Permissive Licence.
---
## [HN-TITLE] 11. 4TB of voice samples just stolen from 40k AI contractors at Mercor
- **Source**: [https://app.oravys.com/blog/mercor-breach-2026](https://app.oravys.com/blog/mercor-breach-2026)
- **Site**: ORAVYS
- **Author**: ORAVYS
- **Submitted**: 2026-04-27 09:57 UTC (Hacker News)
- **HN activity**: 456 points · [168 comments](https://news.ycombinator.com/item?id=47919630)
- **Length**: 1.3K words (~6 min read)
- **Language**: en
[← ORAVYS](https://app.oravys.com/site)
Forensic intelligence // Breach analysis
## 4TB of voice samples were just stolen from 40,000 AI contractors. Here is how to verify if yours is being weaponized.
By the ORAVYS forensic desk Published April 24, 2026 ~7 min read
On April 4, 2026, the extortion group Lapsus$ posted Mercor on its leak site. The dump is reported at roughly four terabytes and bundles a payload that breach analysts have been warning about for two years: voice biometrics paired with the same person's government-issued identity document. According to the leaked sample index, the archive covers more than 40,000 contractors who signed up to label data, record reading passages, and run through verification calls for AI training.
Five contractor lawsuits were filed within ten days of the post. The plaintiffs argue that the company collected voice prints under a "training data" framing without making clear they were also a permanent biometric identifier. The lawsuits matter, but the people whose voices were already exfiltrated have a more immediate question. What does an attacker actually do with thirty seconds of someone's clean read voice plus a scan of their driver's license?
## Why this breach is different
Most voice leaks in the last decade fell into one of two buckets. Either a call center got popped and recordings were stolen with no easy way to map them back to identity. Or an ID-document broker leaked driver's licenses and selfies without any audio attached. Mercor merged both columns. The contractor onboarding pipeline asked for a passport or driver's license scan, then a webcam selfie, then a sit-down voice recording reading scripted prompts in a quiet room. That sequence, in one row of one database, is exactly what a synthetic voice cloning service needs as input.
The Wall Street Journal reported in February 2026 that high-quality voice cloning now requires roughly fifteen seconds of clean reference audio for tools available off the shelf. The Mercor recordings are reported to average two to five minutes of studio-clean speech per contractor. That is far past the threshold. Pair it with a verified ID document and the attacker has both the clone and the credential needed to put the clone to work.
## What attackers can now do with stolen voice data
The threat models below are not speculative. Each is a documented technique already used in the wild before this breach.
- **Bank verification bypass.** Several US and UK banks still treat voiceprint matching as one of two factors. A clone of the account holder reading a challenge phrase clears the audio gate, leaving only a knowledge question that often comes from the same leaked dataset.
- **Vishing the victim's employer.** Calling HR or finance pretending to be the employee to redirect payroll, request a wire, or unlock a workstation. The Krebs on Security archive lists more than two dozen confirmed cases since 2023.
- **Deepfake video calls in the Hong Kong Arup template.** In 2024 a finance worker at Arup wired roughly 25 million dollars after a multi-person deepfake video call. The voices and faces had been built from public footage. Mercor leaked something better than public footage: studio audio plus a verified ID.
- **Insurance claim fraud.** Pindrop reported a 475 percent year-over-year increase in synthetic voice attacks against insurance call centers across 2025. Auto, life, and disability claims are the prime targets because they are settled by phone.
- **Romance and grandparent scams targeting family members.** The FBI Internet Crime Complaint Center logged 2.3 billion dollars in losses for victims aged 60 and over in calendar year 2026. The single fastest-growing category was emergency impersonation calls, where the synthetic voice claims to be a relative in trouble.
## How to check if your voice is being misused
If you ever uploaded a voice sample to Mercor, or to any of the other AI training brokers that operated through 2025, treat your voice the way you would treat a leaked password. You cannot rotate it, but you can change what it unlocks. Here is the short list.
1. **Self-audit your public audio footprint.** Search YouTube, podcast directories, and old Zoom recordings for samples of your voice that are publicly indexable. Take down what you can. The less reference audio is in the open, the less robust an attacker's clone.
2. **Set up a verbal codeword with family and finance contacts.** Pick a phrase that has never been spoken on a recording and never typed in chat. Brief the people who handle money on your behalf. If a call ever asks for a transfer, the codeword is mandatory.
3. **Rotate where voiceprints are still in use.** Google Voice Match, Amazon Alexa Voice ID, Apple personal voice, and any banking voiceprint enrollment can be deleted and replaced. Do that now, ideally from a new recording in a different acoustic environment than the leaked sample.
4. **Tell your bank to disable voiceprint as a verification factor.** Ask in writing for multi-factor authentication that combines an app token or hardware key with a knowledge factor. Many banks let you opt out of voice as a primary factor; few of them advertise it.
5. **Run suspicious recordings through a forensic scanner.** If you receive an audio file or voicemail that claims to be from someone you know and asks for money, access, or urgency, run it through a deepfake detector before acting. ORAVYS offers a free check for the first three samples submitted by breach victims (see the offer below).
## The forensic checklist that experts use
When a sample lands on a forensic analyst's desk, the following artifacts are the first pass. Each is something a synthetic voice tends to get slightly wrong, even when the perceptual quality is high.
- **Codec mismatch.** The audio claims to come from a phone call but the spectral signature does not match any known telephony codec.
- **Breath patterns.** Real speakers inhale at predictable points dictated by phrase length and lung capacity. Synthetic voices often skip breaths or insert them at the wrong syllabic boundary.
- **Micro-jitter.** Natural vocal folds vibrate with small irregularities. Generated audio is often too clean at the millisecond level.
- **Formant trajectory.** Vowel transitions follow physical articulator paths in a real mouth. Cloned voices sometimes take impossible shortcuts between formants.
- **Room acoustics inconsistency.** The reverb signature should be identical from the start of the file to the end. Generated audio is often dry while the splice context is reverberant.
- **Prosody flatness.** Synthetic speech often has narrower pitch and energy variance than the same speaker would have in real conditions.
- **Speech rate stability.** Real humans speed up and slow down with content. Generated speech tends to hold a metronomic rate across long passages.
## What ORAVYS does specifically
- More than 3,000 forensic engines run in parallel on every submitted sample, covering signal, prosody, articulation, codec, and provenance domains.
- AudioSeal watermark detection flags files generated by major commercial voice models when the watermark is preserved, giving a deterministic positive when present.
- An anti-spoofing module trained against the ASVspoof public benchmarks scores the likelihood that a sample was synthesized rather than recorded.
- Biometric processing is RGPD compliant. Audio is never used to train commercial models without explicit consent and is purged on a defined retention schedule.
### Free verification for Mercor breach victims
If you were a Mercor contractor and you believe your voice may already be in circulation, ORAVYS will analyze the first three suspect samples free of charge. You will receive a forensic report covering watermark detection, anti-spoofing score, and the artifact checklist above. No card required, no quota gate.
[Run a forensic check →](https://app.oravys.com/deepfake-detection)
Sources cited in this article: Lapsus$ leak site index (April 2026), Wall Street Journal voice cloning report (February 2026), Pindrop Voice Intelligence Report 2025, FBI IC3 Elder Fraud Report 2026, Krebs on Security archives. Lawsuit references are matters of public record. ORAVYS does not host or redistribute the leaked dataset and does not accept it as input.
---
## [HN-TITLE] 12. Men who stare at walls
- **Source**: [https://www.alexselimov.com/posts/men\_who\_stare\_at\_walls/](https://www.alexselimov.com/posts/men_who_stare_at_walls/)
- **Site**: Alex Selimov
- **Author**: 2026-04-27
- **Published**: 2026-04-27
- **HN activity**: 465 points · [209 comments](https://news.ycombinator.com/item?id=47920074)
- **Length**: 584 words (~3 min read)
- **Language**: en-US

I came across [a video by Simple Lucas](https://www.youtube.com/watch?v=NZD5IFpyDcE&pp=ygUgc3RhcmluZyBhdCB3YWxsIGZvciBwcm9kdWN0aXZpdHk%3D) describing a routine to improve focus and productivity. The routine was basically:
1. Don’t use any screens/entertainment when trying to focus on work.
2. When you start to feel mentally drained, sit and stare at a wall for x minutes to recover focus.
I’ve been trying it, and it’s a very effective (but hard) routine.
## The problem
The core problem is that most people by default are in an information overload. A paper published in 2012 showed that in 2008 the average person was receiving 34 GB of information daily, with a daily information exposure growth rate of about 5.4% per year [1](#fn:1). Extrapolating that trend, we would be at about 87 GB worth of data today. This calculation includes audio, visual, and text data and incorporates quality into the measurement, i.e. 10 minutes of HD video has more information than 10 minutes of 480p video. It’s unclear to me exactly how the quality impacts things, but regardless it is obvious that we are all being drowned in a sea of information.
I certainly go through periods of “brain fog” and lack of focus/motivation. These periods usually go something like:
1. Get a bad night of sleep (up late for an event, kids keep waking me up).
2. Wake up very tired so consume large amounts of caffeine.
3. Have trouble focusing after 2/3 cups so use media while working to dull the pain (music/podcasts) or take more “breaks” (reading hackernews).
4. Stay up late because I’m wired on caffeine and dopamine from scrolling.
5. Go back to 2.
I find these cycles very hard to break out of when I’m in them. The media consumption constitutes a small dopamine hit. Large numbers of small hits puts you in a hole, where you need even more/stronger hits to feel good.
## Disconnecting
The obvious solution is to disconnect from scrolling, but that doesn’t overcome the biggest issue. When I’m in this “brain fog” cycle (and sometimes outside of it), I will find that around 1/2 pm I hit a wall. My head will start hurting, my motivation will be trash, and my productivity significantly degrades. My first instinct is to go for more coffee. That usually lets me keep working, but at a slow/painful pace. While looking for focusing strategies I came across the life-changing solution…
## Stare at a Wall!
After watching Simple Lucas’ experience, I decided to try it when I hit my focus wall.
It worked.
In my attempts, I combined wall staring with a few other concepts I had heard about. First was activating the parasympathetic nervous system by staring at the wall “out-of-focus” and using peripheral vision. Second was incorporating mind blanking which means trying to think of nothing. I tried intervals of 5-10 minutes and when I was done, my focus was back!
What I didn’t expect was how difficult it would be. Sitting for 5-10 minutes staring at a wall without thinking of anything is hard! I relate it somewhat to the feeling I have with working out. Often times I want to avoid it because it’s hard, but I’m always happy when I push through and complete it. It was the exact same experience with the wall staring.
So far I’ve been feeling significant focus/productivity improvements. I’ve also been using some other strategies to improve focus, which I’ll be talking about in a future post. I plan to continue this routine and will update to see how much it has impacted productivity/focus. Thanks for reading!
* * *
1. [https://ijoc.org/index.php/ijoc/article/view/1566](https://ijoc.org/index.php/ijoc/article/view/1566) [↩︎](#fnref:1)
---
## [HN-TITLE] 13. How I leared what a decoupling capacitor is for, the hard way
- **Source**: [https://nbelakovski.substack.com/p/how-i-learned-what-a-decoupling-capacitor](https://nbelakovski.substack.com/p/how-i-learned-what-a-decoupling-capacitor)
- **Site**: Nickolai’s Substack
- **Author**: Nickolai Belakovski
- **Published**: 2026-04-25
- **HN activity**: 36 points · [6 comments](https://news.ycombinator.com/item?id=47905208)
- **Length**: 906 words (~4 min read)
- **Language**: en
I was very excited to get the latest version of my PCB from the manufacturer. This new version had a magnetometer on it, so that I could more accurately track the yaw angle of my drone.
[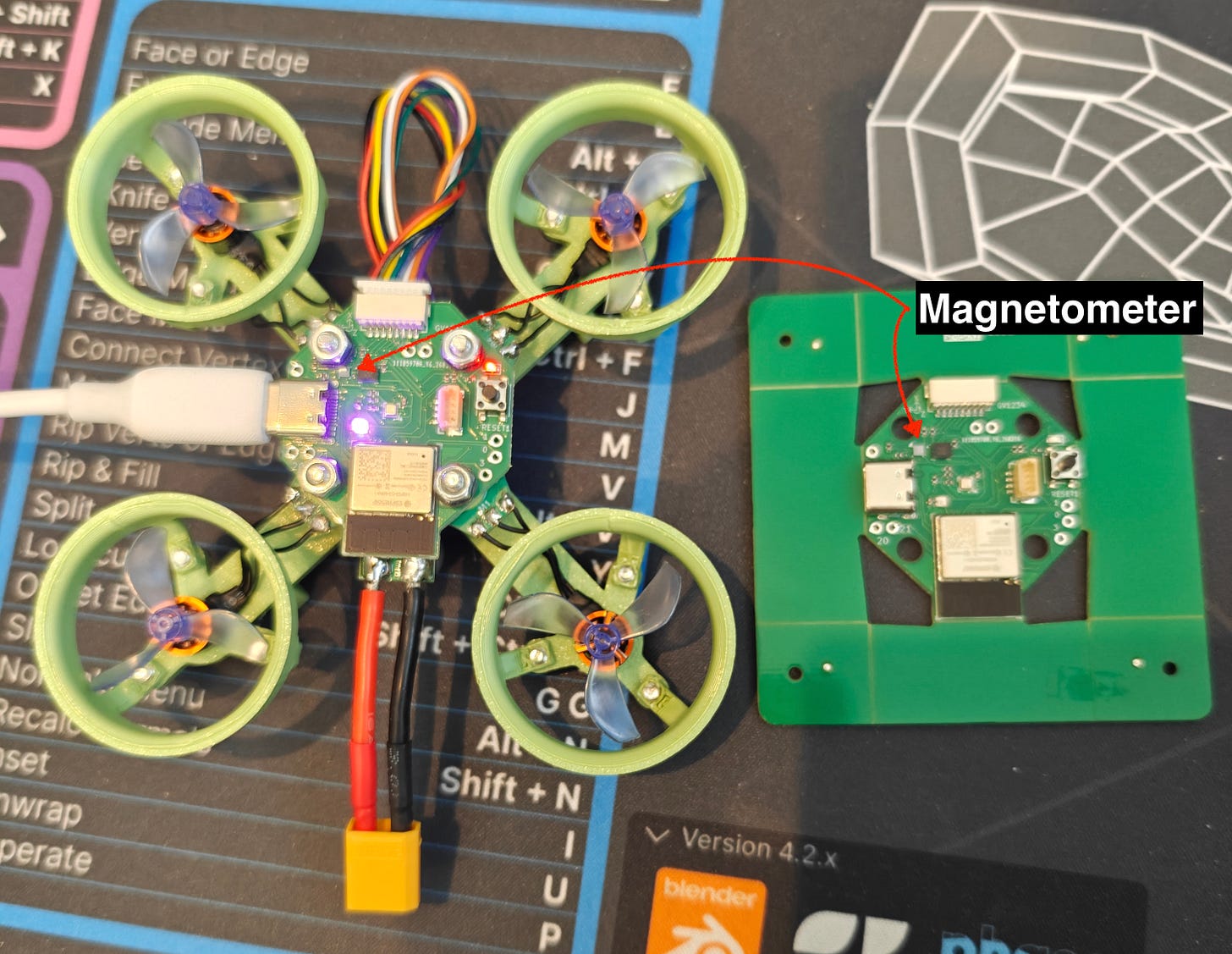](https://substackcdn.com/image/fetch/$s_!qV1Y!,f_auto,q_auto:good,fl_progressive:steep/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2F0e0ee63c-0221-4885-b215-d8c2405b9c9a_3008x2329.jpeg)
The first thing I did was start to program it over USB. I added code for initializing and reading the magnetometer, and I got back some data that seemed correct for the X and Y axes, but the Z axis would read a constant value. I did some light debugging, and learned, among other things, that the Z axis has slightly different internal circuity, but eventually I decided to put a pin in it and focus on other things.
Eventually I had to plug my drone into the battery that would power it in flight, and all of a sudden the magnetometer stopped working completely. I pivoted back to it in an effort to debug it, but nothing worked. I tried to reset the board, I tried to add the code to automatically reset and reinitialize the magnetometer if I hadn’t heard from it for a while, but no matter what I tried it would stay dead when the battery was plugged in.
When I would unplug the battery and plug the USB back in, the magnetometer would recover and work just like it had before. So right away I have to start thinking about what the 3.3V line which powers the magnetometer looks like under USB vs battery.
[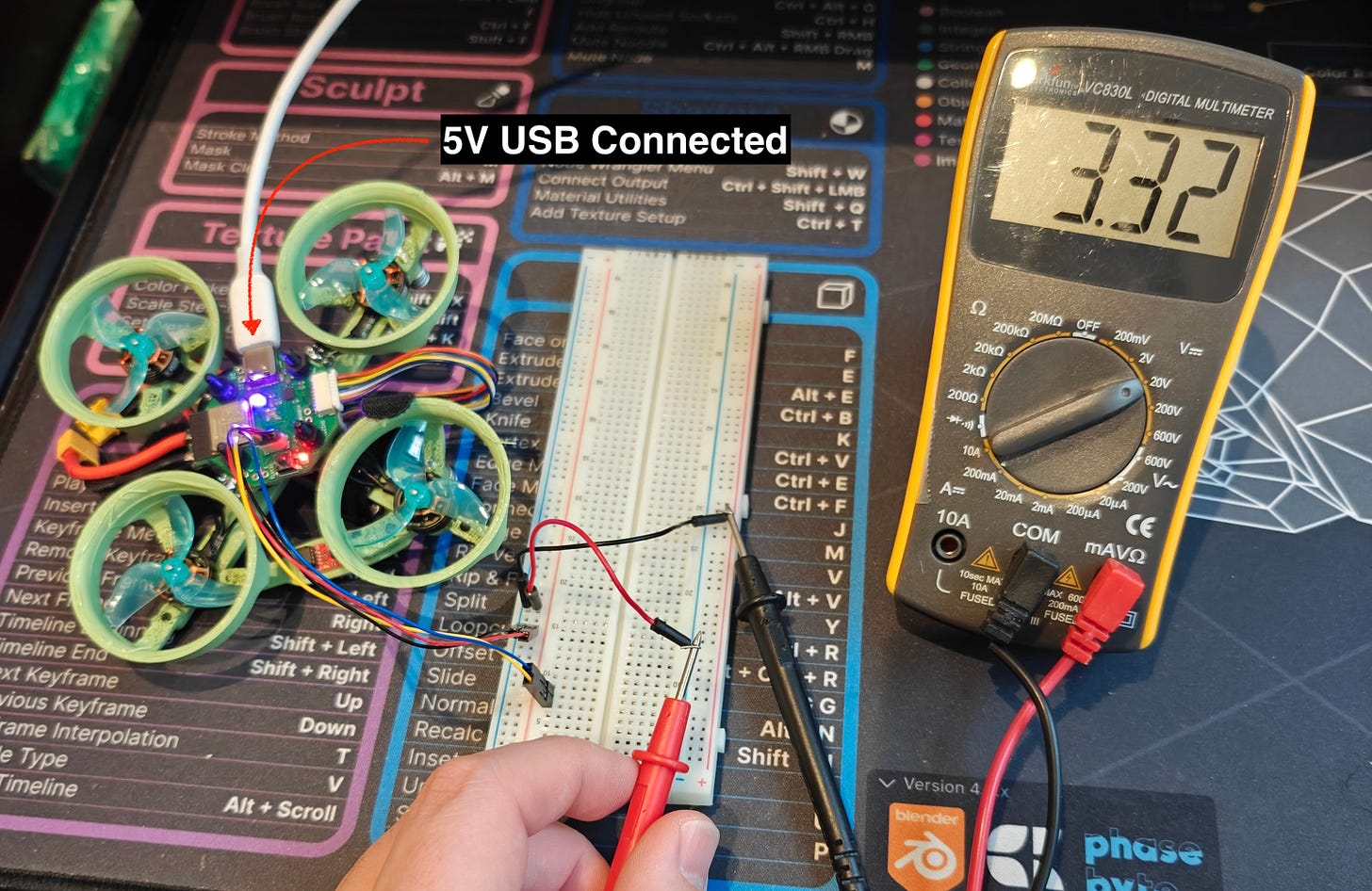](https://substackcdn.com/image/fetch/$s_!dzaA!,f_auto,q_auto:good,fl_progressive:steep/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2F1fdad08c-fca6-4c68-92fd-93b50f74bfe3_3008x1955.jpeg)
A Qwiic connector gives me easy access to the 3.3V bus. Here you can see it’s reading a pretty steady 3.3V
[](https://substackcdn.com/image/fetch/$s_!EhRI!,f_auto,q_auto:good,fl_progressive:steep/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2F39ac8edd-23ea-4a97-a538-ce1ba0e68810_3008x2208.jpeg)
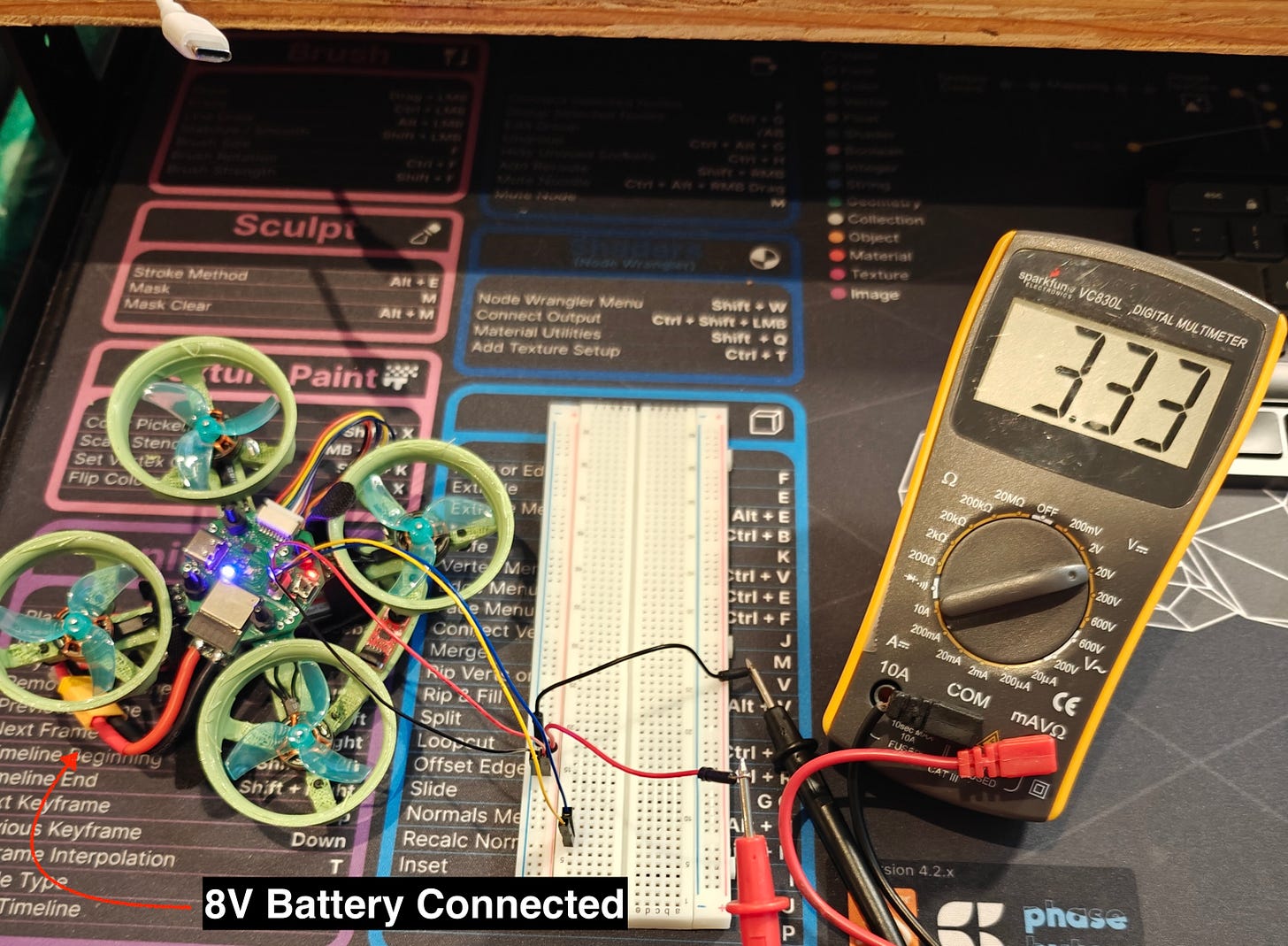
Under battery it similarly reads about 3.3V, and the reading on the multimeter is steady
So does that mean it’s not an issue with the 3.3V bus? Well, not exactly. The multimeter is going to give you a bulk reading, but it’s possible that the line is noisy even though the average reading is 3.3V. The way we get to 3.3V from the initial 5V/8V is through a [SY8113IADC](https://atta.szlcsc.com/upload/public/pdf/source/20200117/C479075_749CE19A0276D274B25CFED6D9E6F64F.pdf) voltage regulator. This is a modern switching regulator which is very efficient, but it achieves that efficiency by, you guessed it, rapidly switching the input supply on and off to effectively drop it down to the desired voltage (as opposed to the older kind of regulator which would just dissipate the energy as heat).
This switching causes ripples in the voltage line, and if we hook up an oscilloscope to the line we should be able to see these ripples in detail.
[](https://substackcdn.com/image/fetch/$s_!uEBh!,f_auto,q_auto:good,fl_progressive:steep/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2Fb029c2d9-e430-4b53-bec1-8286cb22ddc8_3008x2105.jpeg)
This means the 3.3V line ranges from 3.14V to 3.7V. The BMM150 magnetometer is rated for up to 3.6V.
[](https://substackcdn.com/image/fetch/$s_!4RXf!,f_auto,q_auto:good,fl_progressive:steep/https%3A%2F%2Fsubstack-post-media.s3.amazonaws.com%2Fpublic%2Fimages%2Fb278eab3-c943-46b8-b180-7b3b0d4752d4_3008x2171.jpeg)
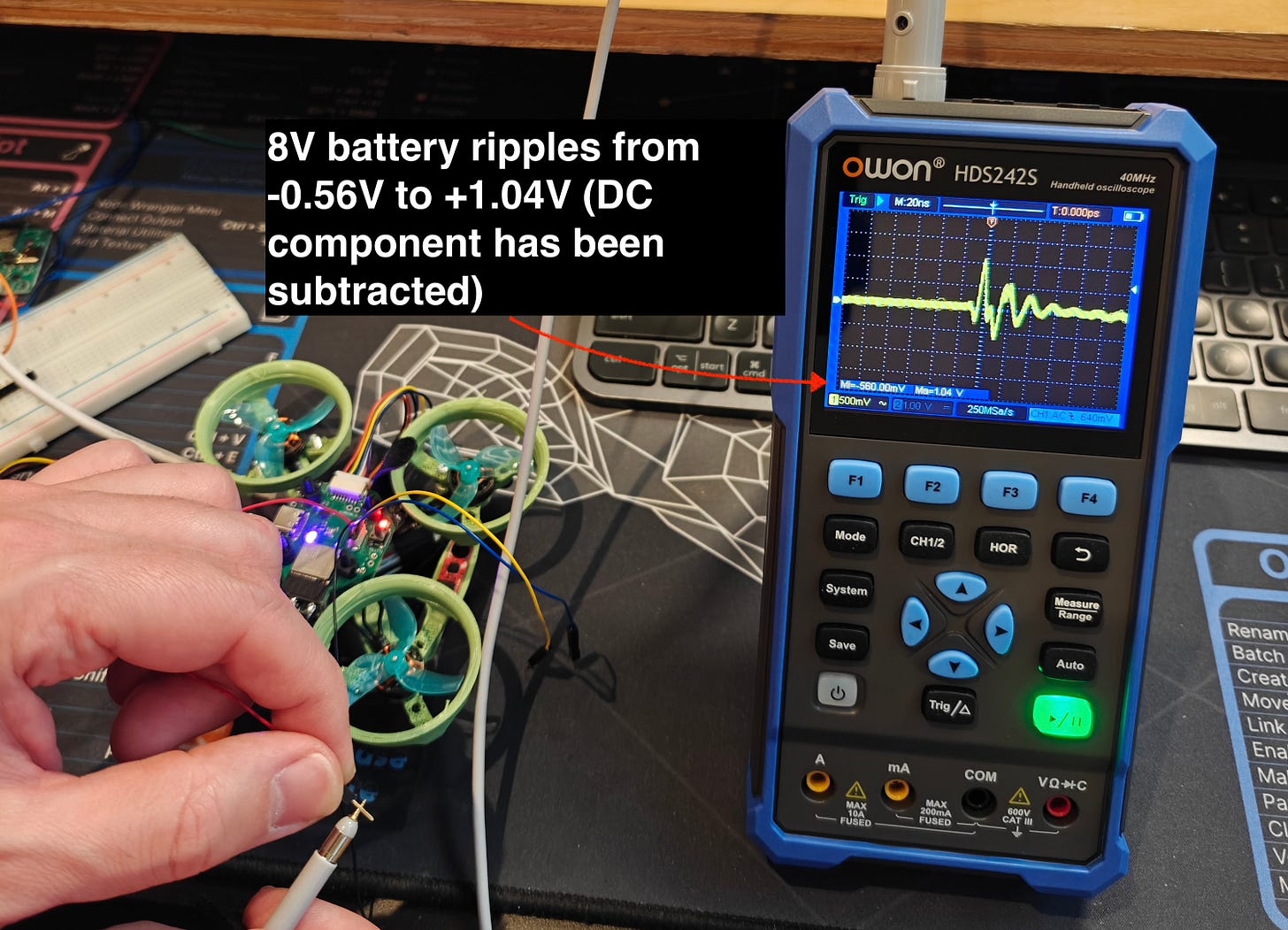
This means the 3.3V line ranges from 2.74V to 4.34V! This must be why the magnetometer simply won’t work on battery power
To get this magnetometer to work on this board, there’s sadly nothing I can really do. At best I could try to solder some tiny wires to the vias on the board near the magnetometer and use those to attach a capacitor between 3.3V and GND as close to the magnetometer as possible but a) it’s likely I’d cause some damage in trying to accomplish this and b) it seems like it would be a very fragile solution.
Fortunately since I had a Qwiic connector on the board, I was able to purchase a magnetometer with a Qwiic interface and attach it. I lose out a little bit since the BMM150 on the board directly interfaces with the BMI270 IMU and synchronizes its readings with the gyroscope/accelerometer readings, but this isn’t critical for what I’m trying to do.
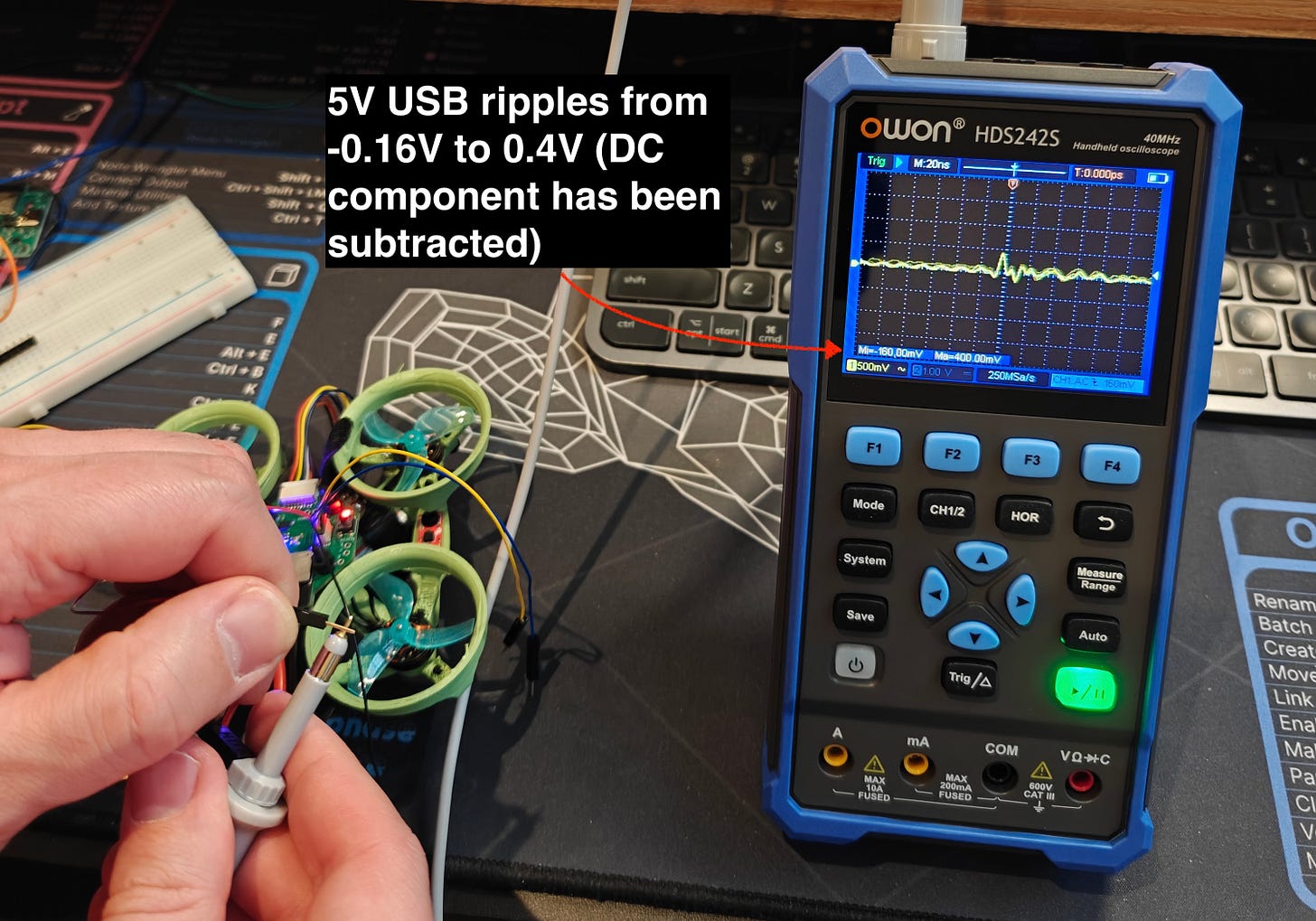
So we can’t exactly fix this, but we can take this as an opportunity to see how a decoupling capacitor cleans up a noisy power signal. The general idea with a decoupling capacitor is that it absorbs high frequency noise in the power line. Take another look at the pictures of the ripples above and notice the “M: 20ns” in the top left corner. This signifies that each vertical dotted line is 20ns apart, so the ripple you see has a frequency of something like 50MHz. This is the sort of noise that a small capacitor right next to the voltage and ground pins of an IC like the BMM150 is supposed to handle, if you put one into your design of course 😅.
I think the most instructive thing is to see in real time how a signal gets cleaned up when you add a decoupling capacitor.
##### For this test I went back to an older version of the PCB. Here it’s powered by 5V USB.
##### And here the board is powered by the 8V battery.
I guess I can’t be sure that the lack of a decoupling capacitor is what kills the BMM150 when I go to battery power. After reviewing my schematic, I noticed I don’t have a decoupling cap for the BMI270, and that seems to work fine, despite also being rated up to 3.6V. That said it’s very clear from this experience that it’s good practice to add decoupling capacitors to all ICs on a board. One of the main reasons I’ve undertaken this project is to learn more about the world of PCBs and embedded engineering and so even though this was frustrating in the moment, it’s exactly the kind of mistake I was hoping to run into. I’ve definitely learned something from this experience and I hope you have as well!
No posts
---
## [HN-TITLE] 14. Show HN: AgentSwift – Open-source iOS builder agent
- **Source**: [https://github.com/hpennington/agentswift](https://github.com/hpennington/agentswift)
- **Site**: GitHub
- **Submitter**: hpen (Hacker News)
- **Submitted**: 2026-04-28 01:14 UTC (Hacker News)
- **HN activity**: 13 points · [4 comments](https://news.ycombinator.com/item?id=47929375)
- **Length**: 357 words (~2 min read)
- **Language**: en
[Download AgentSwift-0.1.zip](https://github.com/hpennington/agentswift/raw/refs/heads/main/AgentSwift-0.1.zip) You must install the dependencies listed below in order for the binary to work. See below for setup commands.
Dependencies:
- Xcode
- Xcode command line tools
- xcodebuildmcp
- openspec
[](https://github.com/hpennington/agentswift/blob/main/screenshot2.png)
[](https://github.com/hpennington/agentswift/blob/main/screenshot.png)
A native macOS app that runs an autonomous AI coding agent for Apple platform development. Describe what you want to build, and AgentSwift uses Claude to discover your project, implement changes, build, run, and validate — without you touching Xcode.
## What it does
[](#what-it-does)
AgentSwift drives a multi-phase agentic workflow:
1. **Discover** — Claude inspects your Xcode project structure and schemes
2. **Implement** — edits source files to match your request
3. **Build** — runs xcodebuildmcp to compile
4. **Launch / Validate** — boots the app on a simulator or macOS, runs UI automation to verify behavior
5. **Archive** — marks the task complete
## Requirements
[](#requirements)
- macOS 26.1+
- Xcode
- Node.js / npm
- An [Anthropic API key](https://console.anthropic.com)
## Dependencies
[](#dependencies)
Install these two CLIs before running the agent:
### xcodebuildmcp
[](#xcodebuildmcp)
Provides build, launch, and UI automation capabilities for Xcode projects.
```
npm install -g xcodebuildmcp
```
### openspec
[](#openspec)
Tracks implementation specs across agent sessions.
```
npm install -g @fission-ai/openspec
```
## Setup
[](#setup)
1. Build and run the app in Xcode.
2. Open **Settings** and enter your Anthropic API key.
3. Select a **Project Folder** (the root of your Xcode project).
4. Optionally pick an **iOS Simulator** from the dropdown.
5. Type what you want to build and press **Cmd+Return**.
On the first run the agent discovers your project's scheme and simulator target. Subsequent runs skip discovery and go straight to implementation.
## Models
[](#models)
Model Use when Claude Opus 4.7 Complex tasks, large codebases Claude Sonnet 4.6 Faster iteration, lighter tasks
## Key behaviors
[](#key-behaviors)
- **Message queuing** — if you send a new message while the agent is running, the latest supersedes earlier ones
- **Build caching** — scheme, project path, and simulator ID are extracted after the first build and reused automatically
- **Error escalation** — the agent attempts one fix on a failure, then surfaces the error to you rather than looping
## Architecture
[](#architecture)
```
AgentSwiftApp.swift — app entry point
ContentView.swift — UI, view models, agentic loop
AnthropicService.swift — Anthropic API client (streaming SSE)
ToolExecutor.swift — bash / read_file / write_file execution
Item.swift — chat message model
```
No external Swift dependencies — pure SwiftUI + Foundation.
---
## [HN-TITLE] 15. Radar Laboratory – Interactive Radar Phenomenology
- **Source**: [https://radarlaboratory.com/](https://radarlaboratory.com/)
- **Site**: radarlaboratory.com
- **Author**: Created and maintained by Hunter Bowden.
- **Submitted**: 2026-04-25 14:24 UTC (Hacker News)
- **HN activity**: 36 points · [0 comments](https://news.ycombinator.com/item?id=47901776)
- **Length**: 6.6K words (~29 min read)
- **Language**: en
RADAR LABORATORY QUICK REF · λ=c/f · R=cτ\_d/2 · ΔR=cτ/2 · f\_d=2v\_r/λ · v\_u=PRF·λ/4 · θ=0.886λ/D
THEORY REFERENCE
ALL KEY RADAR FORMULAS — ORGANIZED BY TOPIC — WITH DERIVATIONS AND CONTEXT
01 — Propagation & Frequency
Fundamental Wavelength Relation
The wavelength λ of an electromagnetic wave is inversely proportional to frequency. Every radar formula contains λ — choosing the operating frequency is the first and most consequential design decision.
λ = c / f c = 3×10⁸ m/s (speed of light) f = carrier frequency (Hz)
λ — wavelength (m) · f — frequency (Hz) · c — 3×10⁸ m/s
PROPAGATIONFUNDAMENTAL
Radar Band Designations
IEEE letter-band designations define standard operating ranges. Band choice determines resolution, attenuation, target interaction, and hardware constraints.
L-band: 1–2 GHz λ ≈ 15–30 cm S-band: 2–4 GHz λ ≈ 7.5–15 cm C-band: 4–8 GHz λ ≈ 3.75–7.5 cm X-band: 8–12 GHz λ ≈ 2.5–3.75 cm Ku-band: 12–18 GHz λ ≈ 1.7–2.5 cm Ka-band: 26–40 GHz λ ≈ 0.75–1.15 cm
BANDSPROPAGATION
Atmospheric Absorption
Water vapor (H₂O) peaks at 22 GHz (~0.18 dB/km) and 183 GHz. Oxygen (O₂) dominates at 60 GHz (~15 dB/km) and 119 GHz. Atmospheric windows at 35, 77, and 94 GHz are exploited by automotive and military radars.
L\_atm (dB) = α(f) × R\_km Two-way loss = 2 × α × R\_km α: dB/km (frequency-dependent)
α — specific attenuation (dB/km) · R\_km — one-way range (km)
PROPAGATIONLOSSES
02 — Range Measurement
Range from Echo Delay
Radar times the two-way travel of a pulse. The round-trip delay τ\_d gives range exactly. Electromagnetic waves travel at c = 3×10⁸ m/s ≈ 150 m/μs (one-way).
R = c · τ\_d / 2 1 μs delay → R = 150 m
τ\_d — round-trip delay (s) · c — 3×10⁸ m/s
RANGEFUNDAMENTAL
Maximum Unambiguous Range
The radar must receive the previous pulse's echo before firing again. If the PRI is too short, a distant echo arrives after the next transmission and is reported at a false closer range.
R\_u = c / (2 · PRF) PRI = 1 / PRF (pulse repetition interval) R\_app = R\_true mod R\_u (folded range)
PRF — pulse repetition frequency (Hz) · PRI — 1/PRF (s)
RANGEAMBIGUITY
03 — Range Resolution & Pulse Compression
Pulse Width Resolution
Two targets closer than ΔR cannot be separated — their echoes overlap in the receiver. The matched filter output width equals cτ/2, which is why resolution and pulse duration are the same formula.
ΔR = c · τ / 2 τ = 1 μs → ΔR = 150 m τ = 10 ns → ΔR = 1.5 m
τ — pulse width (s) · ΔR — minimum resolvable separation (m)
RESOLUTION
Pulse Compression (LFM Chirp)
A chirp sweeps frequency across bandwidth B during pulse duration T. The matched filter compresses the pulse to width 1/B, independent of T. This breaks the energy–resolution trade-off.
ΔR\_compressed = c / (2B) Compression gain: G\_c = B·T Peak sidelobes: −13.2 dB (rect window) −42.7 dB (Hamming window)
B — chirp bandwidth (Hz) · T — pulse duration (s)
PULSE COMPRESSIONLFM
Matched Filter SNR
The matched filter is optimal — it maximizes SNR for any given waveform. The output SNR depends only on the signal energy E and noise spectral density N₀, not on pulse shape.
SNR\_out = 2E / N₀ E = Pt · τ (pulse energy) N₀ = k\_B · T\_sys · F (noise density)
E — signal energy (J) · N₀ — noise spectral density (W/Hz)
MATCHED FILTERSNR
04 — Doppler & Velocity
Doppler Frequency Shift
A moving target compresses (approaching) or stretches (receding) the reflected wavefront, shifting the echo frequency by f\_d. Positive Doppler = closing, negative = opening.
f\_d = 2 · v\_r / λ = 2 · v\_r · f\_c / c v\_r = f\_d · λ / 2 (velocity from Doppler) v\_r = v · cos(θ) (radial component)
v\_r — radial velocity (m/s) · θ — angle from boresight
DOPPLERVELOCITY
Maximum Unambiguous Velocity
The radar samples echo phase once per PRI. The Nyquist limit for phase sampling is π per sample — a target exceeding v\_u aliased to a wrong (lower) apparent velocity. This is the Doppler counterpart of range ambiguity.
v\_u = PRF · λ / 4 Phase advance per PRI: Δφ = π · v\_r / v\_u At v\_r = v\_u: Δφ = π (Nyquist limit) Aliased velocity: v\_app = v\_r mod v\_u
v\_u — max unambiguous velocity (m/s)
VELOCITYAMBIGUITY
05 — PRF & The Range-Doppler Ambiguity
Ambiguity Product — Fixed by Physics
PRF simultaneously sets both R\_u and v\_u in opposite directions. Their product is fixed by the carrier frequency alone — independent of PRF. No single PRF can simultaneously maximize both.
R\_u · v\_u = c² / (8 · f\_c) = λ · c / 8 (in terms of wavelength) Product is CONSTANT for a given frequency.
f\_c — carrier frequency (Hz) · invariant under PRF changes
PRFAMBIGUITYFUNDAMENTAL
Staggered PRF — Resolving Ambiguities
Transmitting alternating PRFs with ratio p:q (p, q coprime) moves blind speeds and ghosted ranges. The Chinese Remainder Theorem extends unambiguous intervals to lcm(R\_u1, R\_u2) in range and lcm(v\_u1, v\_u2) in velocity.
R\_u\_stag = lcm(R\_u1, R\_u2) v\_u\_stag = lcm(v\_u1, v\_u2) Choose PRF ratio p/q where gcd(p,q) = 1
PRF1, PRF2 — staggered pulse rates · p, q — coprime integers
PRFSTAGGERED
06 — Antenna & Beam
Beamwidth
A uniformly illuminated aperture of width D produces a sinc² beam pattern. The 3 dB (half-power) beamwidth in radians is 0.886λ/D. It is always the ratio λ/D that matters — not D or λ independently.
θ\_3dB ≈ 0.886 · λ / D (radians) θ\_3dB ≈ 50.8 · λ / D (degrees) Angular resolution: δ\_az = R · θ\_3dB
D — aperture width (m) · R — range (m) · δ\_az — cross-range resolution
ANTENNABEAMWIDTH
Antenna Gain
Gain G is the ratio of peak radiated intensity to that of an isotropic radiator at the same total power. For a uniformly illuminated aperture, G is proportional to A/λ². Aperture efficiency η accounts for non-uniform illumination (typically 0.6–0.8).
G = η · 4π · A / λ² G = 4π · A\_eff / λ² (A\_eff = η·A) G\_dBi = 10·log₁₀(G)
A — physical aperture area (m²) · η — aperture efficiency · A\_eff — effective area
ANTENNAGAIN
Phased Array — Steering & Grating Lobes
A progressive phase shift φ\_n steers the main beam to angle θ\_s. Element spacing d must satisfy d ≤ λ/2 to push grating lobes outside the visible hemisphere. Violating this creates ambiguous returns at grating lobe angles.
Steering phase: φ\_n = n·2π(d/λ)·sin(θ\_s) Array factor: |AF|² = sin²(Nψ/2)/sin²(ψ/2) ψ = 2π(d/λ)(sinθ − sinθ\_s) Grating lobe: sin(θ\_g) = sin(θ\_s) ± nλ/d Condition for no grating lobe: d ≤ λ/2
BEAMFORMINGPHASED ARRAY
07 — Detection Theory
Hypothesis Testing
Every range cell is tested against two hypotheses: H₀ (noise only) vs H₁ (target + noise). The threshold T sets the trade-off between false alarm probability Pfa and detection probability Pd. No threshold can eliminate both errors simultaneously — the distributions always overlap.
H₀: p(x) = N(0, σ\_n²) \[Gaussian model] H₁: p(x) = N(A\_s, σ\_n²) Pfa = P(x > T | H₀) = Q((T)/σ\_n) Pd = P(x > T | H₁) = Q((T-A\_s)/σ\_n)
DETECTIONNEYMAN-PEARSON
Rayleigh/Rice Model (Envelope Detection)
Real radar receivers use envelope detection, making the noise Rayleigh-distributed (not Gaussian). The Marcum Q₁ function gives Pd for a non-fluctuating target. This is a better model for envelope-detected radar returns. The right model still depends on where in the receiver chain you place the detector and test statistic.
H₀ (noise only): Rayleigh(σ\_n) Pfa = exp(−T²/2σ\_n²) H₁ (target+noise): Rice(A\_s, σ\_n) Pd = Q₁(A\_s/σ\_n, T/σ\_n) \[Marcum Q] Swerling 1: Pd = Pfa^(1/(1+SNR))
DETECTIONRAYLEIGHSWERLING
Coherent Integration
Summing N pulses coherently (phase-aligned) improves SNR by exactly N (linear), or 10 log₁₀(N) dB. This is the fundamental lever for extending detection range without increasing transmit power.
SNR\_coh = N · SNR\_single SNR\_improvement = 10·log₁₀(N) dB Range extension ∝ N^(1/4) Example: N=16 → +12 dB → +88% range
INTEGRATIONDETECTION
08 — CFAR — Constant False Alarm Rate
CA-CFAR Threshold
Cell-Averaging CFAR estimates local noise power from N reference cells surrounding each cell under test (CUT). The threshold scales with the noise estimate, keeping Pfa constant as noise level changes. Guard cells prevent target energy from contaminating the noise estimate.
T = α · mean(reference cell powers) α = N · (Pfa^(−1/N) − 1) Guard cells: typically 2–4 each side Reference cells: typically N = 16–32
α — CFAR scaling factor · N — number of reference cells
CFARDETECTION
CFAR Variants
CA-CFAR fails at clutter edges and in target-rich environments. Variants address specific failure modes at a cost in detection performance.
CA-CFAR: mean of all reference cells GO-CFAR: max(left mean, right mean) \[clutter edges] SO-CFAR: min(left mean, right mean) \[multiple targets] OS-CFAR: k-th order statistic \[non-Rayleigh clutter]
CFARDETECTION
09 — System Parameters & Radar Range Equation
Receiver Noise Power
Thermal noise sets the absolute detection floor. The noise figure F quantifies the excess noise added by the receiver chain above the thermal minimum. The first amplifier (LNA) dominates the cascade.
P\_noise = k\_B · T\_sys · B k\_B = 1.38×10⁻²³ J/K (Boltzmann) T\_sys = T₀(F−1) + T\_ant \[system temp] T₀ = 290 K (standard reference) F\_cascade = F₁ + (F₂−1)/G₁ + ... \[Friis]
k\_B — Boltzmann constant · T\_sys — system noise temperature (K) · B — bandwidth (Hz)
NOISERECEIVER
The Radar Range Equation
The central equation of radar design. Every parameter in the RRE has been covered in the curriculum. The R⁴ dependence means doubling range requires 16× more power, or 4× more antenna gain.
SNR = (Pt · G² · λ² · σ) / ((4π)³ · R⁴ · k\_B · T\_sys · B · F · L) R\_max = \[ Pt·G²·λ²·σ / ((4π)³·SNR\_min·kTBFL) ]^(1/4) In dB: SNR\_dB = Pt\_dBW + 2G\_dBi + 20log(λ) + σ\_dBsm − 30·log(4π) − 40log(R\_m) − 10log(kTBF) − L\_dB
Pt — transmit power (W) · G — antenna gain · σ — RCS (m²) · L — losses (linear)
RANGE EQUATIONFUNDAMENTAL
Radar Cross Section (RCS)
RCS is the effective scattering area of a target — the area of an equivalent isotropic reflector producing the same power density back at the radar. Highly aspect-angle and frequency dependent.
σ = lim(R→∞) 4πR² · |E\_s|²/|E\_i|² Metallic sphere (optical): σ = πr² Flat plate (normal incidence): σ = 4πA²/λ² σ\_dBsm = 10·log₁₀(σ) \[dB sq. meters]
RCSTARGET
10 — Clutter & MTI
Clutter RCS
Ground and sea clutter are distributed targets characterized by the normalized clutter cross-section σ⁰ (sigma-naught) in dB. The total clutter RCS in one range-azimuth cell depends on the cell geometry.
σ\_c = σ⁰ · A\_c A\_c = (c·τ/2) · R · θ\_az \[range-azimuth cell] SCR = σ\_target / σ\_c \[signal-to-clutter] Typical σ⁰: farmland −25 dB, urban −10 dB
CLUTTER
MTI Canceller
Moving Target Indication subtracts consecutive pulse returns. Ground clutter (Doppler ≈ 0) cancels; moving targets survive. The improvement factor (IF) measures cancellation quality.
Single delay: y\[n] = x\[n] − x\[n−1] → H(z) = 1−z⁻¹ Double delay: y\[n] = x\[n] − 2x\[n−1] + x\[n−2] Improvement Factor: IF = SCR\_out / SCR\_in Blind speeds: v\_b = n·PRF·λ/2, n = 1, 2, 3…
MTICLUTTER
11 — FMCW Radar
Beat Frequency & Range
FMCW mixes transmit and receive signals to produce a constant beat frequency proportional to target range. A Doppler component also appears as a frequency offset between up-sweep and down-sweep measurements.
Beat frequency: f\_b = 2·R·B / (c·T) Range from beat: R = f\_b·c·T / (2·B) Range resolution: ΔR = c/(2B) Velocity: v\_r from phase difference between sweeps
B — sweep bandwidth (Hz) · T — sweep period (s) · f\_b — beat frequency
FMCWCW RADAR
12 — STAP & MIMO
STAP Optimal Weights
Space-Time Adaptive Processing jointly nulls clutter and interference in both angle and Doppler. The optimal weight vector maximizes SINR by whitening the interference covariance before steering.
w\_opt = R⁻¹·s / (s^H·R⁻¹·s) R — M×N space-time covariance matrix s — MN×1 space-time steering vector Training requirement: K ≥ 2·M·N (RMB rule)
STAPADAPTIVE
MIMO Virtual Array
MIMO radar transmits orthogonal waveforms from N\_t elements and separates them at N\_r receive elements, synthesizing N\_t×N\_r virtual channels. The virtual aperture has N\_t times the angular resolution of a conventional phased array.
Virtual elements: N\_v = N\_t × N\_r Virtual aperture: L\_v = N\_t · N\_r · d Beamwidth: θ ≈ λ / L\_v DoF gain vs phased array: N\_t times more
MIMOVIRTUAL ARRAY
13 — Target Tracking
Kalman Filter
The Kalman filter is the minimum mean-square-error estimator for linear Gaussian systems. Each cycle alternates between prediction (propagating uncertainty forward) and update (correcting with new measurement).
PREDICT: x\_{k|k-1} = F·x\_{k-1} P\_{k|k-1} = F·P·Fᵀ + Q UPDATE: y\_k = z\_k − H·x\_{k|k-1} \[innovation] S = H·P·Hᵀ + R \[innovation cov] K = P·Hᵀ·S⁻¹ \[Kalman gain] x\_k = x\_{k|k-1} + K·y\_k P\_k = (I−K·H)·P\_{k|k-1}
Q — process noise cov · R — measurement noise cov · F — state transition · H — observation matrix
TRACKINGKALMAN
Tracking Gate & Data Association
An ellipsoidal validation gate selects candidate measurements for each track. The Mahalanobis distance determines whether a measurement falls within the predicted uncertainty ellipsoid.
Gate test: d² = yᵀ·S⁻¹·y ≤ χ²\_{n,P\_g} S = H·P·Hᵀ + R \[innovation covariance] P\_g — gate probability (typically 0.95–0.999) χ²\_{n,P\_g} — chi-squared threshold (n = meas. dim.)
TRACKINGDATA ASSOCIATION
GLOSSARY
RADAR ENGINEERING TERMS — ALPHABETICAL — 57 DEFINITIONS
SEARCH TERMS
A
A-Scope
A radar display that plots received signal amplitude (vertical axis) versus range (horizontal axis). Each target appears as a spike at its corresponding range. The A-scope is the most fundamental radar display and the primary visualization in Modules 02–03.
Ambiguity Function
A 2D function χ(τ, f\_d) that describes the matched filter output for a waveform as a function of both delay (range) and Doppler offset (velocity). The ambiguity function fully characterizes the range-Doppler resolution and sidelobe structure of any waveform — an ideal thumbtack (narrow spike at the origin) is the design goal.
|χ(τ,f\_d)|² = |∫s(t)·s\*(t−τ)·e^(j2πf\_d·t)dt|²
Antenna Aperture
The physical collecting area of an antenna, measured in m². Larger aperture means higher gain and narrower beamwidth for a given wavelength. The effective aperture A\_eff = η·A accounts for illumination taper and feed losses. The relationship G = 4πA\_eff/λ² connects aperture directly to gain.
G = 4π · A\_eff / λ²
Atmospheric Attenuation
The absorption and scattering of radar energy by atmospheric gases, primarily water vapor (H₂O) and oxygen (O₂). Expressed in dB/km, it varies strongly with frequency. At X-band (~10 GHz) attenuation is ~0.01 dB/km; at 60 GHz it reaches 15 dB/km due to oxygen absorption. Both one-way and two-way losses must be budgeted in the Radar Range Equation.
B
Bandwidth
The range of frequencies occupied by a radar signal. For a simple pulse, bandwidth ≈ 1/τ. For a chirp, bandwidth B is the frequency sweep extent and directly sets compressed range resolution ΔR = c/(2B). Wider bandwidth gives finer resolution but requires wider receiver filters (more noise). Bandwidth also sets the noise power floor: P\_noise = k\_B·T·B.
ΔR = c / (2B) P\_noise = k\_B·T·B
Beamforming
The process of combining signals from multiple antenna elements with appropriate phase shifts (and optionally amplitude weights) to produce a directional beam. Beamforming can be implemented in hardware (analog beamforming), digitally after ADC (digital beamforming), or in hybrid architectures. Digital beamforming enables simultaneous multiple beams from the same array.
Beamwidth
The angular width of the main beam of an antenna pattern, typically measured between the half-power (−3 dB) points. For a uniformly illuminated rectangular aperture: θ\_3dB ≈ 0.886λ/D radians. Narrower beamwidth means better angular resolution but requires a larger aperture or higher frequency. The first sidelobe level for a uniform aperture is −13.2 dB below the main lobe peak.
θ\_3dB ≈ 0.886 λ/D (rad) ≈ 50.8 λ/D (deg)
Blind Speed
A target radial velocity at which the MTI canceller erroneously cancels the moving target along with stationary clutter. Blind speeds occur when the target's phase change per PRI is a multiple of 2π, making it appear stationary. The first blind speed is v\_b = PRF·λ/2. Staggered PRF moves blind speeds to different velocities, effectively eliminating most of them in practice.
v\_blind = n · PRF · λ/2, n = 1, 2, 3…
Burn-through Range
The maximum range at which a target's true echo exceeds the jamming noise level, allowing detection despite active noise jamming. Below burn-through range, the radar can detect the target; beyond it, jamming dominates. Lower RCS targets have shorter burn-through ranges. Increasing transmit power, coherent integration, or sidelobe cancellation all extend burn-through range.
C
CA-CFAR Cell-Averaging Constant False Alarm Rate
The most widely used CFAR algorithm. For each range cell under test, it averages the power in N surrounding reference cells and multiplies by a threshold factor α. The threshold rises where noise is high and drops where it is quiet, keeping Pfa constant regardless of noise level. Guard cells adjacent to the CUT prevent the target's own energy from inflating the noise estimate.
T = α · mean(ref cells) α = N·(Pfa^(−1/N) − 1)
CFAR Constant False Alarm Rate
A class of detection algorithms that maintain a constant Pfa regardless of changes in background noise or clutter level, by adaptively setting the detection threshold based on the local environment. The alternative — a fixed threshold — has a Pfa that varies wildly with noise level, producing either excessive false alarms in high-noise regions or missed detections in quiet regions.
Chirp
See [LFM Chirp](). A waveform whose instantaneous frequency sweeps linearly from f₀ to f₀+B over the pulse duration T. Used in pulse compression to achieve fine range resolution (∝ 1/B) while transmitting a long high-energy pulse (∝ T).
Clutter
Any unwanted radar return that is not the target of interest. Ground clutter (land and sea returns), weather clutter (rain, hail), chaff, and birds all produce clutter. Unlike thermal noise (spectrally flat), clutter has spatial and Doppler structure that radar signal processing can exploit. The signal-to-clutter ratio (SCR) determines detectability in clutter-limited environments.
Coherent Integration
The process of summing multiple pulse returns with phase alignment before detection. Because the target signal adds coherently (amplitudes add) while noise adds incoherently (power adds), coherent integration of N pulses improves SNR by N linear (10 log₁₀ N dB). This is fundamentally different from incoherent integration (√N gain in amplitude) and is the primary tool for extending detection range.
SNR\_coh = N · SNR\_single
D
Data Association
The problem of determining which radar measurements belong to which tracked targets. In multi-target environments, measurements from different targets can fall within each other's tracking gates, creating ambiguous correspondence. Algorithms range from Nearest Neighbor (simple, brittle) to JPDA (probabilistic, polynomial) to MHT (optimal, exponential worst-case). Correct association is prerequisite to accurate track maintenance.
Detection Probability Pd
The probability that the radar correctly declares a target present when one actually exists. Pd depends on SNR and the detection threshold T: higher SNR means the target distribution is better separated from the noise distribution. For a given SNR, raising the threshold reduces both Pd (more misses) and Pfa (fewer false alarms). The ROC curve traces all Pd–Pfa pairs for a given SNR.
Pd = P(X > T | H₁) Swerling 1: Pd = Pfa^(1/(1+SNR))
Doppler Effect
The apparent change in frequency of a wave caused by relative motion between source and observer. For radar, a target moving radially at velocity v\_r shifts the echo frequency by f\_d = 2v\_r/λ — positive (upshift) if closing, negative (downshift) if opening. The factor of 2 arises from the round-trip: the radar "hears" the shift on both transmission and reception.
f\_d = 2·v\_r/λ = 2·v\_r·f\_c/c
DRFM Digital Radio Frequency Memory
An electronic warfare device that captures a radar's transmitted waveform digitally, stores it, and retransmits it with controlled modifications (delay, Doppler shift, amplitude changes). DRFM enables sophisticated deception jamming: false targets at controlled ranges and velocities, range-gate pull-off, velocity gate pull-off, and so on. Modern DRFMs operate with GHz bandwidth and nanosecond timing precision.
Duty Cycle
The fraction of time the radar is transmitting: DC = τ · PRF = τ / PRI. High duty cycle means more average power (better SNR) but less time available to receive echoes (reduced range). CW and FMCW radars have duty cycle = 1 (100%), requiring transmit/receive isolation by physical separation or polarization. Pulsed radars typically have duty cycles of 1–10%.
DC = τ · PRF = Pt\_avg / Pt\_peak
E
Electronic Warfare EW
All military and security applications of the electromagnetic spectrum for attack, defense, and support. Electronic Attack (EA) includes jamming, deception, and directed energy. Electronic Protection (EP) includes ECCM techniques like frequency agility, sidelobe blanking, LPI waveforms, and spatial nulling. Electronic Support (ES) is passive interception and signals intelligence. Radar and EW systems are in continuous technological competition.
F
False Alarm Pfa
A detection event where the radar declares a target present when no target exists — noise or clutter exceeds the threshold. Expressed as a probability Pfa = P(noise > T). Even Pfa = 10⁻⁶ (one in a million) generates thousands of false alarms per second at typical radar PRFs (10 kHz PRF × 1000 range bins = 10⁷ tests/second). CFAR keeps Pfa constant; a fixed threshold does not.
Pfa = exp(−T²/2σ\_n²) \[Rayleigh noise]
FMCW Frequency-Modulated Continuous Wave
A radar architecture that transmits a continuous frequency sweep while simultaneously receiving. Mixing transmit and receive signals produces a "beat" frequency directly proportional to target range. FMCW has no minimum range (no T/R switching delay), low peak power (excellent for LPI), compact hardware integration, and simultaneous range-velocity measurement. It is the standard architecture for automotive radar (77 GHz), drone altitude sensors, and industrial level gauges.
f\_beat = 2·R·B/(c·T) ΔR = c/(2B)
Frequency Agility
Changing the radar's carrier frequency pseudo-randomly from pulse to pulse across a wide band. Agility provides: (1) ECCM — spot jammers must spread power across the entire band, reducing J/S; (2) RCS decorrelation — independent scintillation samples improve detection of Swerling 1/2 targets; (3) range sidelobe reduction in synthetic aperture processing. The frequency hop band must be wider than the coherent processing bandwidth.
G
Gain (Antenna) G
The ratio of the antenna's peak radiated power density (in its direction of maximum radiation) to that of a lossless isotropic radiator fed with the same total power. Gain is dimensionless but typically expressed in dBi (dB relative to isotropic). Gain appears as G² in the monostatic Radar Range Equation — once for transmit focusing, once for receive collecting area. A 2× aperture area increase gives +3 dBi gain, which improves maximum detection range by ×2^(1/4) ≈ 19%.
G = η·4πA/λ² (aperture antenna) G\_dBi = 10·log₁₀(G)
Grating Lobe
Secondary maxima in a phased array beam pattern that appear at the same gain as the main lobe when element spacing d > λ/2. A target at a grating lobe angle is completely indistinguishable from a main-beam target, producing a catastrophic ambiguity. All practical phased arrays use d ≤ λ/2 to push grating lobes to sin(θ) > 1 (outside the visible hemisphere). Widening element spacing to reduce cost or increase bandwidth must be traded against grating lobe appearance.
sin(θ\_g) = sin(θ\_s) ± n·λ/d, n=1,2,3… No grating lobes when: d ≤ λ/2
H
Hypothesis Testing H₀ / H₁
The statistical framework underlying all radar detection. H₀ (null hypothesis) = no target present; H₁ (alternative) = target present. The Neyman-Pearson lemma proves that the likelihood ratio test is optimal: it maximizes Pd for a given Pfa. In practice the exact likelihood ratio requires knowledge of the target amplitude distribution, which drives the choice of Swerling model and CFAR variant.
I
Improvement Factor IF
For MTI processors, the improvement factor (also called clutter improvement factor or CIF) is the ratio of signal-to-clutter ratio at the output to that at the input, expressed in dB. A single-delay MTI canceller achieves 30–40 dB IF on ideal stationary clutter. IF is degraded by clutter spectral width (wind-induced motion, antenna scanning, platform motion), receiver phase noise, and A/D quantization errors.
IF = SCR\_out / SCR\_in (linear) IF\_dB = SCR\_out\_dB − SCR\_in\_dB
J
J/S Ratio Jamming-to-Signal Ratio
The ratio of jamming power to target echo power at the radar receiver. A self-screening jammer (on the target aircraft) sees the signal power fall as 1/R⁴ (two-way propagation) while jamming power falls only as 1/R² (one-way propagation). At long range the jammer wins; at short range (burn-through range) the echo dominates. Stand-off jammers (separate platform) see different geometry.
J/S = (Pj·Gj·R²) / (Pt·G²·σ/(4π)·R²\_j) Self-screen: J/S ∝ R² (jammer gains at range)
K
Kalman Filter
A recursive algorithm for optimal state estimation in linear systems with Gaussian noise. Each cycle alternates between prediction (propagating the state estimate and uncertainty forward using the motion model) and measurement update (correcting the prediction using new observations via the Kalman gain). The Kalman gain automatically weights prediction vs measurement based on their respective uncertainties — optimal in the MMSE sense for linear Gaussian systems.
K = P·Hᵀ·(H·P·Hᵀ+R)⁻¹ x←x+K·(z−Hx)
L
LFM Chirp Linear Frequency Modulation
A pulse waveform whose instantaneous frequency sweeps linearly from f₀ to f₀+B over the pulse duration T. The matched filter for an LFM chirp produces a compressed output with width ≈ 1/B — achieving fine resolution independent of pulse length. The time-bandwidth product BT is the pulse compression gain (typically 100–10,000 in modern systems). LFM is the most widely used pulse compression waveform due to its Doppler tolerance and ease of implementation.
ΔR = c/(2B) G\_c = B·T
LPI Low Probability of Intercept
A design philosophy and set of waveform/system techniques that minimize the likelihood of an adversary's electronic support (ES) receiver detecting the radar's transmissions. LPI techniques include: FMCW (low peak power), frequency agility (spread signal across wide band), burst mode operation, low sidelobes, and high antenna directivity. LPI radar sacrifices range or revisit rate to reduce detectability.
M
Matched Filter
A linear filter whose impulse response is the time-reversed complex conjugate of the transmitted waveform. The matched filter maximizes the output SNR for any given waveform and is provably optimal under the Neyman-Pearson criterion. Its output is the cross-correlation of the received signal with the transmitted template; peaks in the output correspond to target ranges. The width of the peak equals the inverse signal bandwidth — which is why range resolution equals c/(2B).
h(t) = s\*(T−t) SNR\_out = 2E/N₀
MIMO Radar Multiple-Input, Multiple-Output
A radar architecture that transmits orthogonal waveforms from multiple antennas simultaneously. Each receive element separates the orthogonal transmit waveforms using matched filters, creating N\_t×N\_r virtual receive channels. The resulting virtual aperture has N\_t times more elements than a conventional phased array of the same physical size, providing superior angular resolution and degrees of freedom for STAP and parameter estimation.
Virtual DoF = N\_t × N\_r
MTI Moving Target Indication
A signal processing technique that cancels stationary clutter by subtracting consecutive pulse returns. The clutter, nearly identical between pulses, cancels; moving targets change phase each PRI and survive. Single-delay MTI uses H(z)=1−z⁻¹ (notch at DC); double-delay MTI deepens the notch. MTI is the simplest form of Doppler processing and is the predecessor to modern pulse-Doppler and STAP processors.
y\[n] = x\[n] − x\[n−1] → H(e^jω) = 1 − e^{−jω}
N
Noise Figure F or NF
A measure of the excess noise added by a receiver component or chain above the thermal noise floor. Defined as F = SNR\_in / SNR\_out (linear). A perfect noiseless receiver has F = 1 (0 dB). Real LNAs achieve 0.5–3 dB; system noise figures of 3–10 dB are common. The Friis cascade formula shows that the first element (LNA) contributes most: cooling or improving it gives the largest system benefit.
F\_total = F₁ + (F₂−1)/G₁ + (F₃−1)/(G₁G₂) + …
O
Off-Boresight Angle
The angular separation between the radar's boresight (main beam axis) and the direction to a target of interest. Antenna gain falls off as the off-boresight angle increases, following the one-way pattern G(θ). At the 3 dB beamwidth (θ₃dB/2 off boresight), gain drops by 3 dB one-way (6 dB two-way), reducing SNR significantly. Targets at large off-boresight angles may be seen only through sidelobes.
G(θ) ≈ G₀ · sinc²(πDsinθ/λ) (uniform aperture)
Operating Frequency f₀, λ
The carrier frequency at which a radar transmits. Operating frequency determines wavelength (λ = c/f₀), which in turn affects range resolution, Doppler sensitivity, antenna size, and atmospheric propagation losses. Common radar bands: L-band (1–2 GHz, long-range surveillance), S-band (2–4 GHz, weather/ATC), C-band (4–8 GHz, weather), X-band (8–12 GHz, fire control/imaging), Ka-band (27–40 GHz, automotive).
λ = c / f₀ (c ≈ 3×10⁸ m/s)
P
Phased Array
An antenna array in which the phase (and optionally amplitude) of the signal applied to each element is individually controlled to steer and shape the beam electronically, without mechanical movement. Phase steering can redirect the beam in microseconds — versus tens of milliseconds for mechanically scanned antennas. Phased arrays enable simultaneous multiple beams, adaptive nulling, and rapid interleaving of different radar modes.
PPI Scope Plan Position Indicator
A radar display that presents a top-down (azimuth vs range) 2D map of the surveillance area. The radar antenna rotates (or the beam scans electronically), and each range-azimuth cell is mapped to a pixel. Targets appear as bright spots at their true geographic positions. PPI is the standard display for air traffic control, weather radar, and naval surveillance systems.
PRF Pulse Repetition Frequency
The number of pulses transmitted per second (Hz). PRF simultaneously sets maximum unambiguous range (R\_u = c/2PRF) and maximum unambiguous velocity (v\_u = PRF·λ/4) in opposite directions — increasing PRF extends velocity coverage but reduces range coverage. The PRF ambiguity product R\_u·v\_u = c²/(8f\_c) is fixed by physics. Three PRF regimes: low PRF (range unambiguous), medium PRF (both ambiguous), high PRF (velocity unambiguous).
R\_u = c/(2·PRF) v\_u = PRF·λ/4
Pulse Compression
A waveform processing technique that transmits a long coded pulse (for energy) but achieves the range resolution of a short pulse (for resolution). The most common form uses an LFM chirp; phase-coded waveforms (Barker, Frank codes) are also used. The time-bandwidth product B·T is the compression gain: the ratio of compressed to uncompressed pulse width. Pulse compression decouples the energy–resolution trade-off that limits simple pulsed radars.
G\_c = B·T ΔR = c/(2B) (compressed)
Q
Quadrature Sampling I/Q
A signal representation using two components sampled in phase quadrature (90° apart): In-phase (I) and Quadrature (Q). Together they form a complex-valued signal s(t) = I(t) + jQ(t) that preserves both amplitude and phase of the radar return. I/Q sampling enables coherent processing, Doppler estimation, and unambiguous phase measurement. Modern radars digitize I and Q directly at IF or use digital downconversion from RF samples.
s(t) = I(t) + jQ(t) A = √(I²+Q²) φ = atan2(Q,I)
R
Radar Cross Section RCS, σ
The effective scattering area of a target, defined as the area of an equivalent perfectly reflecting isotropic sphere that would return the same power to the radar. RCS depends on target shape, size, material, orientation (aspect angle), and radar frequency. Typical values: aircraft 1–10 m² (0–10 dBsm), stealth aircraft ~0.001 m² (−30 dBsm), ship 1,000–100,000 m² (30–50 dBsm). A 10 dB reduction in RCS cuts maximum detection range by ~44%.
σ\_dBsm = 10·log₁₀(σ) sphere: σ = πr²
Radar Range Equation RRE
The fundamental equation relating radar detection range to system parameters. It expresses the received SNR as a function of transmit power, antenna gain, wavelength, RCS, range, and noise. The R⁴ dependence (two-way propagation squared) is the central challenge of long-range radar — doubling range requires 16× more power or 4× more antenna area. All Phase I–II modules build toward this single equation.
SNR = Pt·G²·λ²·σ / ((4π)³·R⁴·kTBFL)
ROC Curve Receiver Operating Characteristic
A plot of detection probability Pd versus false alarm probability Pfa for all possible threshold values at a given SNR. Every point on the curve represents a different threshold setting. Higher SNR shifts the ROC curve up and to the left (better performance). The ideal ROC curve passes through (Pfa=0, Pd=1) — a perfect detector. The area under the ROC curve (AUC) is a single-number performance metric.
S
SAR Synthetic Aperture Radar
A radar imaging technique that exploits the motion of the platform (aircraft, satellite) to synthesize a virtual aperture far larger than the physical antenna. By coherently processing echoes collected over a long along-track distance L\_s, SAR achieves cross-range resolution δ\_cr ≈ D/2 — independent of range and wavelength. SAR enables centimeter-resolution imaging from low Earth orbit and is used for terrain mapping, change detection, and reconnaissance.
δ\_cr ≈ D/2 (focused SAR, D = physical aperture)
Sidelobes
Secondary maxima of the antenna beam pattern or matched filter output that appear outside the main lobe. Antenna sidelobes allow targets or jammers at off-boresight angles to produce returns that appear to come from the main beam direction. Matched filter range sidelobes create false peaks around a real target. Both are controlled by window functions (tapering) at a cost in main lobe width. The first sidelobe of a uniform aperture/rectangle window is −13.2 dB; Hamming gives −42.7 dB.
SNR Signal-to-Noise Ratio
The ratio of target signal power to noise power at the detector input, expressed linearly or in dB. SNR is the primary determinant of detection performance: higher SNR means better separation of the target and noise distributions, enabling either higher Pd at a given Pfa, or the same Pd at lower Pfa. The SNR required for a given (Pd, Pfa) pair is the detection threshold and is read from ROC curves or Albersheim's equation.
SNR\_dB = 10·log₁₀(P\_signal / P\_noise)
Staggered PRF
A technique using two or more alternating pulse repetition frequencies with incommensurate ratios to extend the unambiguous range and velocity coverage beyond what any single PRF can achieve. Based on the Chinese Remainder Theorem: the extended unambiguous intervals are the least common multiples of the individual intervals. Staggered PRF also moves MTI blind speeds — a target visible at one PRF is likely visible at the other.
STAP Space-Time Adaptive Processing
An adaptive signal processing technique that simultaneously exploits spatial (array element) and temporal (pulse) degrees of freedom to cancel interference. For an airborne radar, STAP places a 2D null in angle-Doppler space along the clutter ridge (where ground clutter appears at all Doppler shifts proportional to platform velocity × angle cosine). STAP generalizes both beamforming (spatial only) and MTI (temporal only) into a unified framework.
w\_opt = R⁻¹·s / (sᴴ·R⁻¹·s)
Swerling Models
A set of four statistical models (Sw0–Sw4) describing how target RCS fluctuates over time. Sw0: non-fluctuating (steady RCS). Sw1: exponential RCS distribution, scan-to-scan decorrelation (multiple glints — aircraft body). Sw2: exponential, pulse-to-pulse decorrelation. Sw3: chi-squared 4 DoF, scan-to-scan (dominant scatterer). Sw4: chi-squared 4 DoF, pulse-to-pulse. Fluctuating targets (Sw1–4) require more SNR than non-fluctuating for Pd > 0.5 — the diversity loss.
Sw1: Pd = Pfa^(1/(1+SNR\_avg))
System Losses L
All signal power losses that reduce the received SNR below what the Radar Range Equation would predict for an ideal system. Includes: feed and transmission line losses, antenna pointing loss, signal processing losses (range and Doppler straddle losses), A/D quantization loss, matched filter mismatch, propagation losses (rain, atmospheric), and system integration losses. Typically 3–10 dB total. Must be measured and budgeted for each specific system design.
T
Thermal Noise
Random electrical noise generated by the thermal agitation of electrons in any resistive component above absolute zero. It is irreducible — the fundamental detection floor for every radar. The available noise power from a resistor at temperature T over bandwidth B is P = k\_B·T·B. At 290 K and 1 MHz bandwidth, this is −114 dBm. Reducing system temperature (cooling the LNA), narrowing bandwidth, or narrowing the noise figure are the only ways to lower the floor.
P\_noise = k\_B · T · B k\_B = 1.38×10⁻²³ J/K
Tracking Gate Validation Gate
An ellipsoidal region in measurement space centered on a track's predicted position, used to determine which measurements could plausibly have originated from that track. Measurements falling inside the gate are candidates for association; those outside are rejected. The gate size is set by the innovation covariance S and a chi-squared threshold corresponding to the desired gate probability P\_g. Small gates reduce false association but risk missing the true measurement when prediction is imprecise.
d² = yᵀ·S⁻¹·y ≤ χ²\_{n,Pg}
U
Unambiguous Range R\_u
The maximum target range at which the radar can correctly identify the echo as belonging to the most recent pulse. Beyond R\_u, the echo arrives after the next pulse has been transmitted and is incorrectly attributed to that later pulse, causing the radar to report a "folded" shorter range. R\_u is set by the PRF: R\_u = c/(2·PRF). Increasing PRF extends Doppler coverage but shrinks R\_u.
R\_u = c / (2·PRF)
Unambiguous Velocity v\_u
The maximum radial velocity the radar can unambiguously measure. Beyond v\_u, the target's Doppler phase advance per PRI exceeds π radians (the Nyquist limit), causing the velocity to alias to an incorrect lower value or wrong direction. v\_u is set by the PRF and wavelength: v\_u = PRF·λ/4. Decreasing PRF (to extend range) shrinks v\_u.
v\_u = PRF · λ / 4
W
Window Function Taper, Weighting
An amplitude weighting applied to an array aperture (spatial window) or pulse bandwidth (spectral window) to reduce sidelobes at the cost of slightly widened main lobe. Common windows: Rectangular (no taper — highest sidelobes −13.2 dB, narrowest main lobe), Hamming (−42.7 dB sidelobes, 1.46× wider main lobe), Taylor (adjustable −25 to −50 dB sidelobes), Chebyshev (equiripple — minimum main lobe width for given sidelobe level). Used in both antenna pattern shaping and range/Doppler processing.
ABOUT RADAR LABORATORY
A VISUAL COURSE FOR BUILDING PRACTICAL RADAR INTUITION
PURPOSE
**Radar Laboratory is an interactive learning environment for engineers who need to understand radar behavior without treating the sensor as a black box.**
Each module pairs a visual scene with a plot, live readouts, and a short explanation. The goal is to make the physical behavior visible first, then connect that behavior to the equations.
The material is written for new engineers, systems engineers, analysts, and software developers who work around radar systems but may not have formal RF or electrical-engineering training.
LEARNING PATH
The course starts with the measurements radar makes directly, then builds toward performance limits, detection, digital processing, and advanced phenomenology.
- **Measurement foundations:** electromagnetic waves, range timing, PRF, range resolution, Doppler, and ambiguity.
- **Waveforms, targets, and aperture:** pulse energy, matched filtering, RCS, antenna gain, arrays, beamwidth, and scanning.
- **Performance and propagation:** noise, SNR, coherent integration, the radar range equation, free-space loss, atmospheric loss, multipath, horizon, and clutter.
- **Detection:** thresholding, clutter-limited detection, and CFAR.
- **Digital processing:** IQ data, Fourier transforms, fast/slow time, range bins, Doppler spectra, and range-Doppler maps.
- **Advanced phenomenology:** trajectories, scatterers, ISAR, MTI, STAP, and electronic attack.
ACCURACY AND SCOPE
The simulations use standard radar relationships and simplified engineering models. They are intended for training, communication, and first-order intuition.
Radar Laboratory is not a replacement for a validated radar performance model, mission-analysis tool, hardware test, or scenario-specific simulation. When a module uses a simplification, the module text states the main assumption and keeps the core physical relationship intact.
HOW TO USE IT
- Start with the scene and identify what is physically happening.
- Move one control at a time.
- Watch the plot and readouts change.
- Use the checkpoint to confirm the takeaway.
- Use the theory page when you want the equation in context.
REFERENCE BASIS
The content follows standard radar, antenna, detection, propagation, and DSP references, including Skolnik, Richards, Levanon & Mozeson, Balanis, Van Trees, Nathanson, Ward, Kay, Oppenheim & Schafer, Stimson, and ITU-R recommendations P.676, P.838, and P.530.
Equations are used to support intuition. Engineering decisions should still be checked against authoritative references and validated models.
TECHNOLOGY
Radar Laboratory is a single-file HTML application using HTML5 Canvas, CSS, and vanilla JavaScript. It can be hosted as a static site or opened locally for demonstration and training.
HTML5 CANVAS VANILLA JS SINGLE FILE STATIC SITE READY
---
## [HN-TITLE] 16. Networking changes coming in macOS 27
- **Source**: [https://eclecticlight.co/2026/04/23/networking-changes-coming-in-macos-27/](https://eclecticlight.co/2026/04/23/networking-changes-coming-in-macos-27/)
- **Site**: The Eclectic Light Company
- **Submitter**: pvtmert (Hacker News)
- **Published**: 2026-04-23
- **HN activity**: 211 points · [185 comments](https://news.ycombinator.com/item?id=47923010)
- **Length**: 584 words (~3 min read)
- **Language**: en
Apple seldom gives advanced notice of significant changes coming in the next major version of macOS, before its first beta-release at WWDC. One significant exception to this are changes to networking that could impact enterprise users. This year, with just over six weeks to go before that first beta of macOS 27, we already have two warnings of what might be coming.
#### AFP and network storage
Apple made SMB its primary file-sharing protocol in OS X 10.9 Mavericks, over 12 years ago, and has repeatedly told us that support for its predecessor AFP will be removed in the future. It repeated those warnings with macOS Sequoia 15.5, but still hasn’t confirmed when AFP will be lost.
Those who are most likely to be affected by this are still using Time Capsules, or elderly NAS systems that don’t support SMB3. As removal of AFP support won’t be retrospective, provided that none of your Macs will be upgraded to macOS 27, you’ll still be able to use AFP for your file shares and Time Machine backups. But if you have an Apple silicon Mac and AFP support is dropped from macOS 27, that would leave you unable to upgrade without replacing your network storage.
#### TLS and servers
Most recently, Apple [has warned](https://support.apple.com/126655) that a future version of macOS, and its device OSes, will require connections to certain servers to be made using at least TLS 1.2, with additional requirements. I’m grateful to Rich Trouton’s [Der Flounder blog](https://derflounder.wordpress.com/2026/04/21/apple-enforcing-stricter-network-security-requirements-for-future-versions-of-apples-platform-operating-systems/) for drawing attention to this.
Although Apple carefully avoids being too specific, it warns that this change could come “as early as the next major software release”, although one of the purposes behind its support article is to gauge the impact the change might have on its enterprise customers. If there would be major problems, it may decide to delay its introduction.
This change is more technical, and largely applies to servers involved in supporting MDM, DDM, Automated Device Enrolment, app distribution and installation, and Apple software updates. Fortunately, if you run a local Content Caching server, that *won’t* be affected.
Unlike the removal of AFP, it’s far harder to tell whether a connection to a server complies with the new rules, which require:
- support for TLS 1.2 or later, with TLS 1.3 recommended,
- use of ATS-compliant ciphersuites,
- presentation of valid certificates meeting ATS standards.
The most reliable way to check is to audit connections made to each server, by screening log entries from the Mac or device. That’s further complicated by the fact that the log doesn’t normally gather the information that’s required. So the first step is to install a network diagnostics logging profile available from Apple. The [support article](https://support.apple.com/126655) explains how to collect a logarchive using `sysdiagnose`, and provides a monster predicate to extract relevant entries:
`"p=appstoreagent|appstored|managedappdistributionagent|managedappdistributiond|ManagedClient|ManagedClientAgent| mdmclient|mdmd|mdmuserd|MuseBuddyApp|NanoSettings|Preferences|profiled|profiles|RemoteManagementAgent| remotemanagementd|Setup|'Setup Assistant'|'System Settings'|teslad|TVSettings|TVSetup|XPCAcmeService AND s=com.apple.network AND m:'ATS Violation'|'ATS FCPv2.1 violation'"`
And yes, Apple is encouraging system administrators to copy and paste a command into Terminal, because there’s no GUI app in macOS that could be used to do that, although you can use it in Ulbow, and I suspect in LogUI with a little modification.
If you’re within the scope of this proposed change, you’ll need to read [Rich Trouton’s account](https://derflounder.wordpress.com/2026/04/21/apple-enforcing-stricter-network-security-requirements-for-future-versions-of-apples-platform-operating-systems/), and Apple’s [full article](https://support.apple.com/126655). I wish you the best of luck. As with AFP, this change shouldn’t apply retrospectively.
#### Timescale
- 27.0 developer beta due on 8 June 2026
- 27.0 public beta due around 8 July 2026
- 27.0 release most probably in mid-September 2026, only five months away.
---
## [HN-TITLE] 17. Spanish archaeologists discover trove of ancient shipwrecks in Bay of Gibraltar
- **Source**: [https://www.theguardian.com/science/2026/apr/15/hidden-treasures-spanish-archaeologists-discover-trove-of-ancient-shipwrecks-in-bay-of-gibraltar](https://www.theguardian.com/science/2026/apr/15/hidden-treasures-spanish-archaeologists-discover-trove-of-ancient-shipwrecks-in-bay-of-gibraltar)
- **Site**: The Guardian
- **Author**: Sam Jones
- **Published**: 2026-04-15
- **HN activity**: 83 points · [14 comments](https://news.ycombinator.com/item?id=47907175)
- **Length**: 1.0K words (~5 min read)
- **Language**: en
Spanish archaeologists exploring the bay that curves between the southern port of Algeciras and the Rock of Gibraltar have documented the wrecks of more than 30 ships that came to grief near the Pillars of Hercules between the fifth century BC and the second world war.
Over the millennia, the bay, which sits at the north end of the strait of Gibraltar that separates [Europe](https://www.theguardian.com/world/europe-news) from Africa, has swallowed everything from Phoenician and Roman vessels to British, Spanish, Venetian and Dutch ships – as well as the odd aeroplane.
A [three-year project](https://produccioncientifica.uca.es/documentos/69a09b7dbb968f5c160c69bf) led by the University of Cádiz has now identified 151 archaeological sites in the bay, among them 134 shipwrecks. To date, the researchers and their colleagues from the University of Granada have worked to document 34 of those wrecks.

A pair of team members uses a suction hose to clean sediment from a wreck in the Bay of Algeciras. Photograph: Felipe Cerezo Andreo
The oldest is that of a Punic era ship dating to the fifth century BC, while other finds include 23 Roman ships, two late Roman ships, four medieval ships and 24 vessels from the early modern period.
Between them, the sunken items – which include an agile and fearsome 18th-century Spanish gunboat and the engine and propeller of a plane from the 1930s – tell the story of war, trade, exploration and settlement in and around one of the most strategically important waterways in the world.
Felipe Cerezo Andreo, a professor of archaeology at the University of Cádiz who led the investigation, which is called Project Herakles, said that area has long been a watery crossroads.
“It’s one of those bottlenecks through which ships have always had to pass, whether on commercial shipping routes, voyages of discovery, or due to armed conflicts,” he said.

An outlined wreck is seen from above a few metres offshore in the Bay of Algeciras. Photograph: Alejandro Mañas
“There are really few places in the Mediterranean that have this kind of concentration and such a significant variety of archaeological remains, especially in terms of different cultures or different nations. We have Dutch, Venetian, Spanish, and of course English ships – ships of practically every nationality – because they all passed through the strait, whether heading out to the Atlantic for trade, or entering the Mediterranean from northern Europe or other regions.”
Cerezo said the researchers were particularly excited to have documented three medieval vessels that could shed light on seafaring during the late period of Islamic rule in southern [Spain](https://www.theguardian.com/world/spain).
Although the team has come across large ships from the 16th and 17th centuries, one of the most exciting finds has been the wreck of the Puente Mayorga IV, a small, late 18th-century gunboat of a type used for rapid, stealthy attacks on British ships of the line around Gibraltar. The attack craft would often disguise themselves as fishing boats before flinging off their netting and firing their prow-mounted cannon at their enemies.

A book-shaped box that was found in the wreck of the 18th-century Spanish gunboat Puente Mayorga IV. Photograph: Felipe Cerezo Andreo
Despite being frequently mentioned in contemporary reports, such boats have been little studied by archaeologists.
Cerezo himself was delighted to come across one of the Puente Mayorga IV’s less obvious treasures during an excavation. What he initially took to be a miraculously preserved book turned out to be a book-shaped wooden box with a hollow space inside.
“At first, we thought it could be used to hide documents, and we thought it might have something to do with espionage,” said the archeologist. “Was the officer who carried it mapping the position of an enemy vessel?” Sadly not. After careful examination, the box turned out to contain a pair of wooden combs, suggesting the officer may have been more preoccupied with grooming than spying.
Cerezo and his colleagues hope the Andalucían regional government and Spain’s culture ministry will act to preserve and protect the sites in the Bay of Algeciras – known to English-speakers as the Bay of Gibraltar – which are at risk from port development, dredging and dock construction. The climate emergency is already proving a threat, bringing both rising sea levels that are [altering sediment layers and exposing archaeological sites](https://www.marinebiodiversity.ca/rising-seas-are-washing-away-ancient-underwater-treasures-heres-what-scientists-are-doing/#google_vignette), and [an invasive algae that grows over rocks and wrecks alike](https://www.ceab.csic.es/en/lalga-asiatica-rugulopteryx-okamurae-detectada-al-litoral-de-barcelona/).

A member of the Herakles Project team examines a wreck in the Bay of Algeciras. Photograph: Herakles Project/Supplied
In order to share their finds and raise awareness of the importance of preserving them, the researchers have made virtual models and 360-degree videos of the sites, which they share with the public online and in local museums and town halls.
“We bring these goggles so that people who don’t dive can put them on and have a dryland diving experience,” said Cerezo. “Although people sometimes imagine they’re going to see [a wrecked treasure ship like the Unicorn in Tintin](https://www.tintin.com/en/albums/red-rackham-s-treasure), the sites tend not to be that well preserved. The state of them can sometimes be a bit disappointing, but it’s important that people know what’s going on. And showing this to people creates a demand for the protection of these sites.”
[map of the Bay of Gibraltar](https://interactive.guim.co.uk/uploader/embed/2026/04/algecirasbay-zip/giv-32554pl2OCOGZ7luo/)
The waters of the bay offer an unparalleled microcosm of thousands of years of maritime and cultural development, said Cerezo.
“What we have here is a very small space that allows us to analyse the evolution of maritime history throughout practically the whole of the Iberian peninsula and north Africa.
“It tells us a story that we sometimes forget, which is that maritime societies, or peoples who have lived in coastal areas, have had a very intense relationship with the sea and have lived on the sea. And being able to study these kinds of archaeological remains – to document them, to learn about them in situ and not just through the objects that sometimes end up in a museum, but to understand them in their context – allows us to carry out that process of reconstruction and to tell the story of these people.”
---
## [HN-TITLE] 18. The woes of sanitizing SVGs
- **Source**: [https://muffin.ink/blog/scratch-svg-sanitization/](https://muffin.ink/blog/scratch-svg-sanitization/)
- **Site**: muffin.ink
- **Submitter**: varun\_ch (Hacker News)
- **Submitted**: 2026-04-27 15:31 UTC (Hacker News)
- **HN activity**: 190 points · [76 comments](https://news.ycombinator.com/item?id=47922957)
- **Length**: 2.9K words (~13 min read)
- **Language**: en
Scratch has a long history of SVG-related vulnerabilities. The source of these is that Scratch parses user-generated (ie. attacker-controlled) content into an `
```
This [was fixed](https://github.com/scratchfoundation/scratch-svg-renderer/commit/78cc7ea22887cdb2d3e3a00b23557a37251632f8) by using a regular expression to remove script tags.
Surely, with this change, SVGs are now fully safe and will require no further security fixes.
## 2020: XSS via oversights in previous fix (CVE-2020-7750)
In 2020, [apple502j discovered](https://scratch.mit.edu/discuss/topic/449794/) that XSS is still possible. It turns out that the previous fix is utterly defective and can be bypassed by capitalizing `